nist.gov
Updated:
2021-06-13 14:08:06 UTC (1312 days ago)
Go to most recent »
Notices
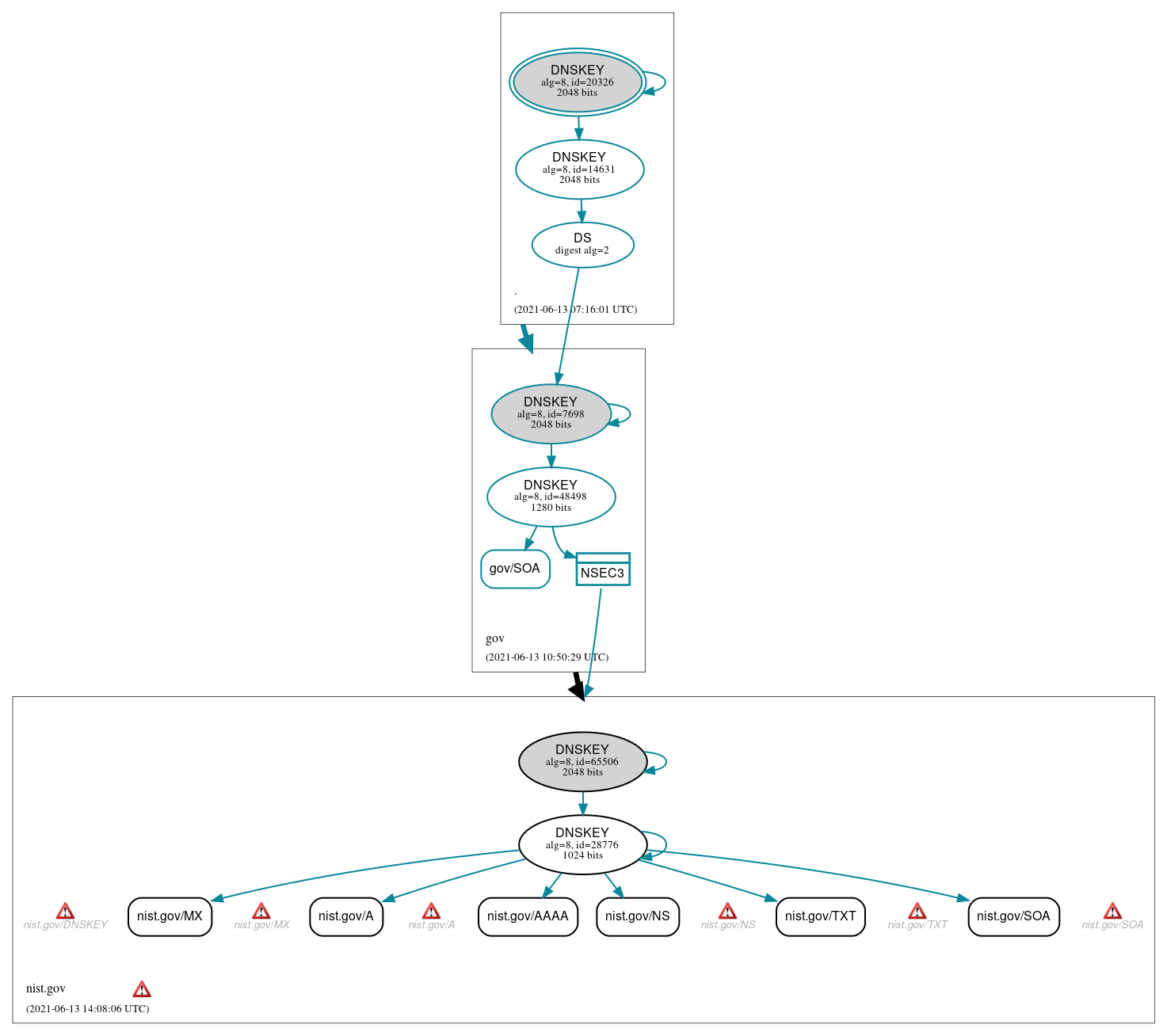
DNSSEC Authentication Chain
 RRset status
RRset status
Insecure (6)
- nist.gov/A
- nist.gov/AAAA
- nist.gov/MX
- nist.gov/NS
- nist.gov/SOA
- nist.gov/TXT
Secure (1)
- gov/SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Insecure (2)
- nist.gov/DNSKEY (alg 8, id 28776)
- nist.gov/DNSKEY (alg 8, id 65506)
Secure (6)
- ./DNSKEY (alg 8, id 14631)
- ./DNSKEY (alg 8, id 20326)
- NSEC3 proving non-existence of nist.gov/DS
- gov/DNSKEY (alg 8, id 48498)
- gov/DNSKEY (alg 8, id 7698)
- gov/DS (alg 8, id 7698)
 Delegation status
Delegation status
Insecure (1)
- gov to nist.gov
Secure (1)
- . to gov
 Notices
Notices
Errors (17)
- NSEC3 proving non-existence of nist.gov/DS: An iterations count of 0 must be used in NSEC3 records to alleviate computational burdens. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of nist.gov/DS: An iterations count of 0 must be used in NSEC3 records to alleviate computational burdens. See RFC 9276, Sec. 3.1.
- nist.gov zone: The server(s) were not responsive to queries over TCP. See RFC 1035, Sec. 4.2. (129.6.13.3, 129.6.13.4, 132.163.4.10)
- nist.gov zone: The server(s) were not responsive to queries over UDP. See RFC 1035, Sec. 4.2. (132.163.4.11, 2610:20:6005:13::3, 2610:20:6005:13::4, 2610:20:6b01:4::10, 2610:20:6b01:4::11)
- nist.gov/A: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (132.163.4.11, 2610:20:6005:13::3, 2610:20:6005:13::4, 2610:20:6b01:4::10, 2610:20:6b01:4::11, UDP_-_NOEDNS_)
- nist.gov/DNSKEY: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (129.6.13.3, 132.163.4.10, UDP_-_NOEDNS_)
- nist.gov/DNSKEY: No response was received from the server over UDP (tried 4 times). See RFC 1035, Sec. 4.2. (129.6.13.3, 129.6.13.4, UDP_-_EDNS0_512_D_KN)
- nist.gov/MX: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (129.6.13.3, 129.6.13.4, UDP_-_NOEDNS_)
- nist.gov/MX: No response was received from the server over UDP (tried 4 times). See RFC 1035, Sec. 4.2. (129.6.13.3, UDP_-_EDNS0_512_D_KN)
- nist.gov/NS: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (132.163.4.11, 2610:20:6005:13::3, 2610:20:6005:13::4, 2610:20:6b01:4::10, 2610:20:6b01:4::11, UDP_-_NOEDNS_)
- nist.gov/SOA: No response was received from the server over TCP (tried 3 times). See RFC 1035, Sec. 4.2. (129.6.13.3, 129.6.13.4, 132.163.4.10, TCP_-_EDNS0_4096_D_N)
- nist.gov/SOA: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (132.163.4.10, UDP_-_NOEDNS_)
- nist.gov/TXT: No response was received from the server over TCP (tried 4 times). See RFC 1035, Sec. 4.2. (129.6.13.3, TCP_-_EDNS0_4096_D_KN)
- 4vp1mr0c2d.nist.gov/A has errors; select the "Denial of existence" DNSSEC option to see them.
- nist.gov/CNAME has errors; select the "Denial of existence" DNSSEC option to see them.
- nist.gov/DS has errors; select the "Denial of existence" DNSSEC option to see them.
- nist.gov/DNSKEY has errors; select the "Denial of existence" DNSSEC option to see them.
Warnings (4)
- NSEC3 proving non-existence of nist.gov/DS: The salt value for an NSEC3 record should be empty. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of nist.gov/DS: The salt value for an NSEC3 record should be empty. See RFC 9276, Sec. 3.1.
- 4vp1mr0c2d.nist.gov/A has warnings; select the "Denial of existence" DNSSEC option to see them.
- nist.gov/DS has warnings; select the "Denial of existence" DNSSEC option to see them.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.