www.reulitz.de
Updated:
2025-04-07 12:09:30 UTC (19 days ago)
Go to most recent »
Notices
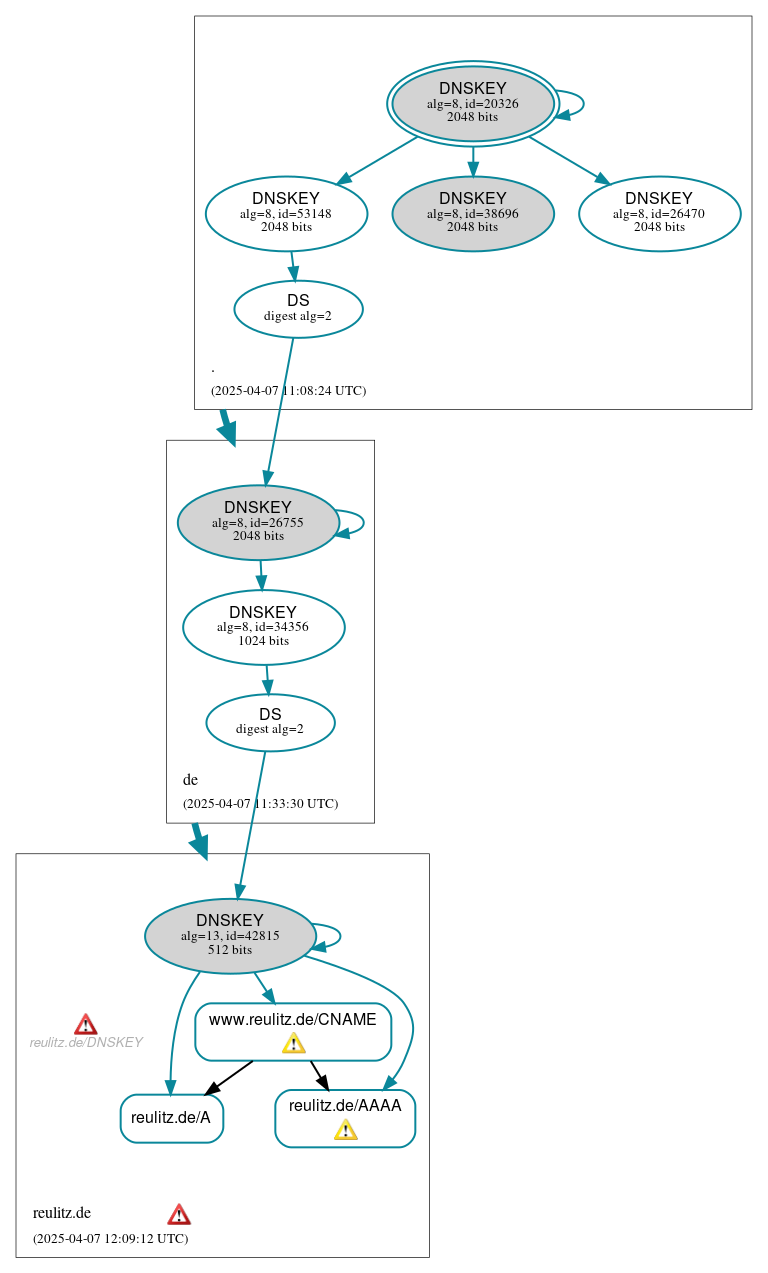
DNSSEC Authentication Chain
 RRset status
RRset status
Secure (3)
- reulitz.de/A
- reulitz.de/AAAA
- www.reulitz.de/CNAME
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (9)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 26470)
- ./DNSKEY (alg 8, id 38696)
- ./DNSKEY (alg 8, id 53148)
- de/DNSKEY (alg 8, id 26755)
- de/DNSKEY (alg 8, id 34356)
- de/DS (alg 8, id 26755)
- reulitz.de/DNSKEY (alg 13, id 42815)
- reulitz.de/DS (alg 13, id 42815)
 Delegation status
Delegation status
Secure (2)
- . to de
- de to reulitz.de
 Notices
Notices
Errors (2)
- reulitz.de zone: The server(s) responded over TCP with a malformed response or with an invalid RCODE. See RFC 1035, Sec. 4.1.1. (37.120.176.220)
- reulitz.de/DNSKEY: No response was received from the server over UDP (tried 4 times). See RFC 1035, Sec. 4.2. (37.120.176.220, UDP_-_EDNS0_512_D_KN)
Warnings (2)
- reulitz.de/AAAA: No response was received from the server over UDP (tried 6 times) until the COOKIE EDNS option was removed (however, this server appeared to respond legitimately to other queries with the COOKIE EDNS option present). See RFC 6891, Sec. 6.1.2. (46.38.237.208, UDP_-_EDNS0_4096_D_KN)
- www.reulitz.de/CNAME: No response was received until the UDP payload size was decreased, indicating that the server might be attempting to send a payload that exceeds the path maximum transmission unit (PMTU) size. See RFC 6891, Sec. 6.2.6. (46.38.237.208, UDP_-_EDNS0_4096_D_KN)





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.