www.dynhost.ml
Updated:
2022-12-28 12:08:45 UTC (1170 days ago)
Go to most recent »
Notices
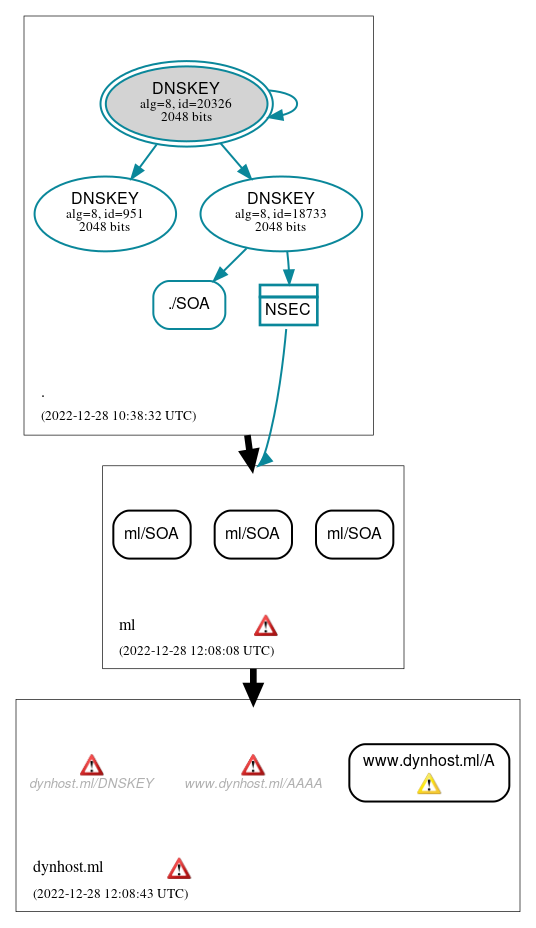
DNSSEC Authentication Chain
 RRset status
RRset status
Insecure (4)
- ml/SOA
- ml/SOA
- ml/SOA
- www.dynhost.ml/A
Secure (1)
- ./SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (4)
- ./DNSKEY (alg 8, id 18733)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 951)
- NSEC proving non-existence of ml/DS
 Delegation status
Delegation status
Insecure (2)
- . to ml
- ml to dynhost.ml
 Notices
Notices
Errors (5)
- dynhost.ml zone: The server(s) were not responsive to queries over UDP. See RFC 1035, Sec. 4.2. (193.254.196.206)
- dynhost.ml/DNSKEY: The response (92 bytes) was malformed. (176.9.168.4, UDP_-_EDNS0_512_D_KN, UDP_-_NOEDNS_)
- ml zone: The server(s) were not responsive to queries over UDP. See RFC 1035, Sec. 4.2. (2a04:1b00::1)
- www.dynhost.ml/AAAA: The response (96 bytes) was malformed. (176.9.168.4, UDP_-_NOEDNS_)
- dynhost.ml/CNAME has errors; select the "Denial of existence" DNSSEC option to see them.
Warnings (1)
- www.dynhost.ml/A: The response (64 bytes) was malformed until EDNS was disabled. See RFC 6891, Sec. 6.2.6. (176.9.168.4, UDP_-_EDNS0_4096_D_KN)





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.