tsp.gov
Updated:
2022-01-26 19:00:33 UTC (1033 days ago)
Go to most recent »
Notices
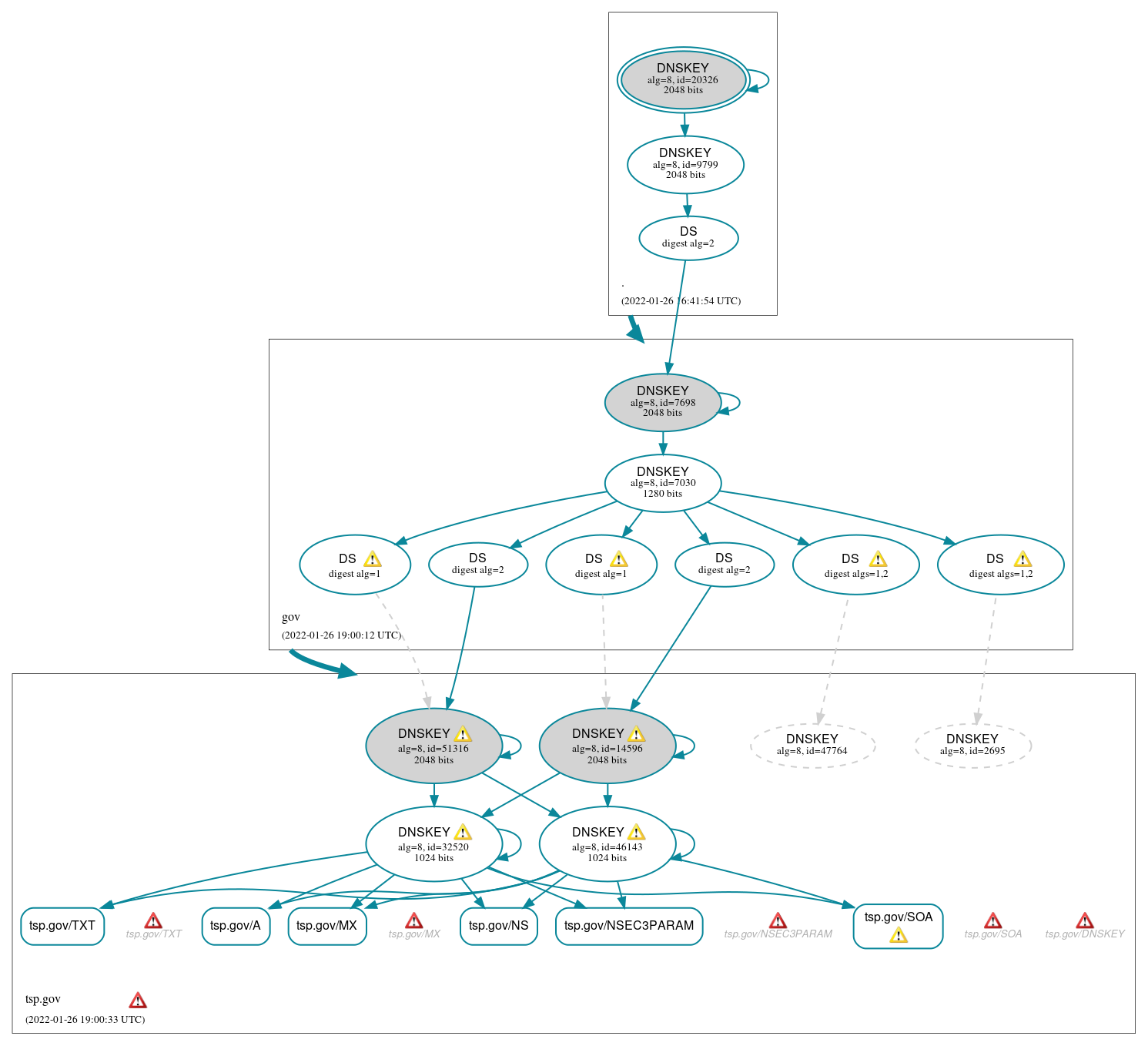
DNSSEC Authentication Chain
 RRset status
RRset status
Secure (6)
- tsp.gov/A
- tsp.gov/MX
- tsp.gov/NS
- tsp.gov/NSEC3PARAM
- tsp.gov/SOA
- tsp.gov/TXT
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (15)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 9799)
- gov/DNSKEY (alg 8, id 7030)
- gov/DNSKEY (alg 8, id 7698)
- gov/DS (alg 8, id 7698)
- tsp.gov/DNSKEY (alg 8, id 14596)
- tsp.gov/DNSKEY (alg 8, id 32520)
- tsp.gov/DNSKEY (alg 8, id 46143)
- tsp.gov/DNSKEY (alg 8, id 51316)
- tsp.gov/DS (alg 8, id 14596)
- tsp.gov/DS (alg 8, id 14596)
- tsp.gov/DS (alg 8, id 2695)
- tsp.gov/DS (alg 8, id 47764)
- tsp.gov/DS (alg 8, id 51316)
- tsp.gov/DS (alg 8, id 51316)
Non_existent (2)
- tsp.gov/DNSKEY (alg 8, id 2695)
- tsp.gov/DNSKEY (alg 8, id 47764)
 Delegation status
Delegation status
Secure (2)
- . to gov
- gov to tsp.gov
 Notices
Notices
Errors (12)
- tsp.gov zone: The server(s) were not responsive to queries over TCP. See RFC 1035, Sec. 4.2. (149.101.82.185, 149.101.82.186, 149.101.182.186)
- tsp.gov/DNSKEY: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (149.101.82.186, UDP_-_NOEDNS_)
- tsp.gov/MX: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (149.101.82.186, 149.101.182.186, UDP_-_NOEDNS_)
- tsp.gov/NSEC3PARAM: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (149.101.82.185, 149.101.82.186, 149.101.182.186, UDP_-_NOEDNS_)
- tsp.gov/SOA: No response was received from the server over TCP (tried 3 times). See RFC 1035, Sec. 4.2. (149.101.82.185, 149.101.82.186, 149.101.182.186, TCP_-_EDNS0_4096_D_N)
- tsp.gov/SOA: No response was received from the server over TCP (tried 5 times). See RFC 1035, Sec. 4.2. (149.101.182.185, TCP_-_EDNS0_4096_D_N)
- tsp.gov/SOA: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (149.101.82.185, 149.101.82.186, 149.101.182.186, UDP_-_NOEDNS_, UDP_-_NOEDNS__0x20)
- tsp.gov/TXT: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (149.101.82.186, UDP_-_NOEDNS_)
- tsp.gov/DNSKEY has errors; select the "Denial of existence" DNSSEC option to see them.
- oike1sf24b.tsp.gov/A has errors; select the "Denial of existence" DNSSEC option to see them.
- tsp.gov/AAAA has errors; select the "Denial of existence" DNSSEC option to see them.
- tsp.gov/CNAME has errors; select the "Denial of existence" DNSSEC option to see them.
Warnings (21)
- tsp.gov/DNSKEY (alg 8, id 14596): No response was received until the UDP payload size was decreased, indicating that the server might be attempting to send a payload that exceeds the path maximum transmission unit (PMTU) size. See RFC 6891, Sec. 6.2.6. (149.101.182.185, UDP_-_EDNS0_4096_D_KN)
- tsp.gov/DNSKEY (alg 8, id 32520): No response was received until the UDP payload size was decreased, indicating that the server might be attempting to send a payload that exceeds the path maximum transmission unit (PMTU) size. See RFC 6891, Sec. 6.2.6. (149.101.182.185, UDP_-_EDNS0_4096_D_KN)
- tsp.gov/DNSKEY (alg 8, id 46143): No response was received until the UDP payload size was decreased, indicating that the server might be attempting to send a payload that exceeds the path maximum transmission unit (PMTU) size. See RFC 6891, Sec. 6.2.6. (149.101.182.185, UDP_-_EDNS0_4096_D_KN)
- tsp.gov/DNSKEY (alg 8, id 51316): No response was received until the UDP payload size was decreased, indicating that the server might be attempting to send a payload that exceeds the path maximum transmission unit (PMTU) size. See RFC 6891, Sec. 6.2.6. (149.101.182.185, UDP_-_EDNS0_4096_D_KN)
- tsp.gov/DS (alg 8, id 14596): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- tsp.gov/DS (alg 8, id 14596): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- tsp.gov/DS (alg 8, id 14596): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- tsp.gov/DS (alg 8, id 14596): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- tsp.gov/DS (alg 8, id 47764): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- tsp.gov/DS (alg 8, id 47764): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- tsp.gov/DS (alg 8, id 47764): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- tsp.gov/DS (alg 8, id 47764): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- tsp.gov/DS (alg 8, id 51316): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- tsp.gov/DS (alg 8, id 51316): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- tsp.gov/DS (alg 8, id 51316): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- tsp.gov/DS (alg 8, id 51316): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- tsp.gov/SOA: No response was received until the UDP payload size was decreased, indicating that the server might be attempting to send a payload that exceeds the path maximum transmission unit (PMTU) size. See RFC 6891, Sec. 6.2.6. (149.101.182.185, UDP_-_EDNS0_4096_D_KN, UDP_-_EDNS0_4096_D_KN_0x20)
- tsp.gov/DNSKEY has warnings; select the "Denial of existence" DNSSEC option to see them.
- oike1sf24b.tsp.gov/A has warnings; select the "Denial of existence" DNSSEC option to see them.
- tsp.gov/AAAA has warnings; select the "Denial of existence" DNSSEC option to see them.
- tsp.gov/CNAME has warnings; select the "Denial of existence" DNSSEC option to see them.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.