polkam.go.id
Updated:
2023-08-11 12:16:43 UTC (2 years ago)
Go to most recent »
Notices
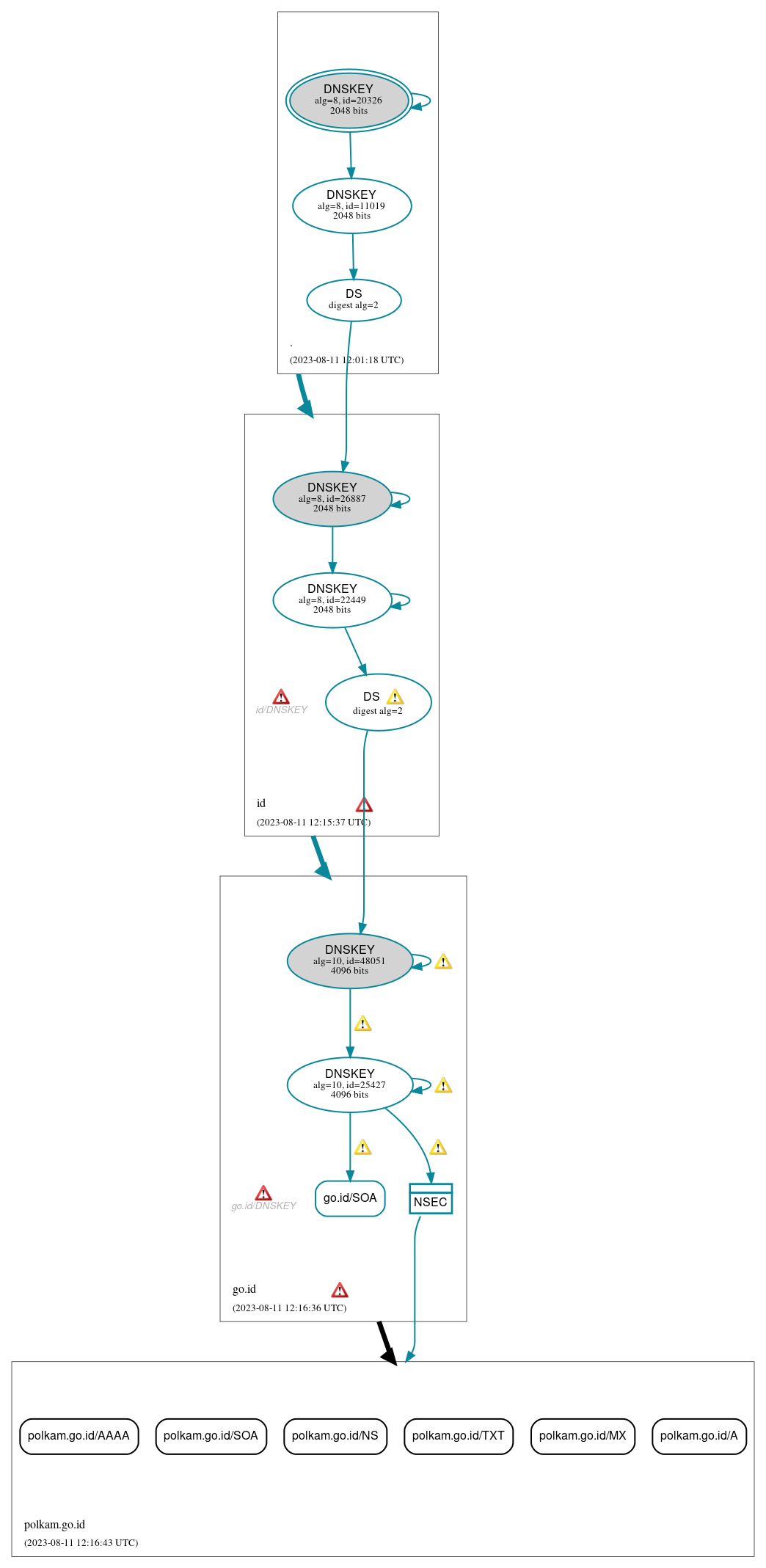
DNSSEC Authentication Chain
 RRset status
RRset status
Insecure (6)
- polkam.go.id/A
- polkam.go.id/AAAA
- polkam.go.id/MX
- polkam.go.id/NS
- polkam.go.id/SOA
- polkam.go.id/TXT
Secure (1)
- go.id/SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (9)
- ./DNSKEY (alg 8, id 11019)
- ./DNSKEY (alg 8, id 20326)
- NSEC proving non-existence of polkam.go.id/DS
- go.id/DNSKEY (alg 10, id 25427)
- go.id/DNSKEY (alg 10, id 48051)
- go.id/DS (alg 10, id 48051)
- id/DNSKEY (alg 8, id 22449)
- id/DNSKEY (alg 8, id 26887)
- id/DS (alg 8, id 26887)
 Delegation status
Delegation status
Insecure (1)
- go.id to polkam.go.id
Secure (2)
- . to id
- id to go.id
 Notices
Notices
Errors (8)
- go.id zone: The server(s) were not responsive to queries over TCP. See RFC 1035, Sec. 4.2. (45.126.57.57, 103.19.177.177)
- go.id zone: The server(s) were not responsive to queries over UDP. See RFC 1035, Sec. 4.2. (2402:ee80:b::b, 2402:ee80:c::c, 2402:ee80:d::d)
- go.id/DNSKEY: No response was received from the server over TCP (tried 12 times). See RFC 1035, Sec. 4.2. (45.126.57.57, 103.19.177.177, TCP_-_EDNS0_4096_D_KN)
- go.id/DNSKEY: No response was received from the server over TCP (tried 7 times). See RFC 1035, Sec. 4.2. (2001:df5:4000:4::4, TCP_-_EDNS0_4096_D)
- id zone: The server(s) responded over TCP with a malformed response or with an invalid RCODE. See RFC 1035, Sec. 4.1.1. (103.19.177.177)
- id zone: The server(s) were not responsive to queries over UDP. See RFC 1035, Sec. 4.2. (2402:ee80:b::b, 2402:ee80:c::c, 2402:ee80:d::d)
- id/DNSKEY: No response was received from the server over UDP (tried 13 times). See RFC 1035, Sec. 4.2. (103.19.177.177, UDP_-_EDNS0_4096_D_KN)
- id/DNSKEY: No response was received from the server over UDP (tried 4 times). See RFC 1035, Sec. 4.2. (2001:df5:4000:4::4, UDP_-_EDNS0_512_D_KN)
Warnings (11)
- RRSIG NSEC proving non-existence of polkam.go.id/DS alg 10, id 25427: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 10 (RSASHA512). See RFC 8624, Sec. 3.1.
- RRSIG go.id/DNSKEY alg 10, id 25427: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 10 (RSASHA512). See RFC 8624, Sec. 3.1.
- RRSIG go.id/DNSKEY alg 10, id 25427: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 10 (RSASHA512). See RFC 8624, Sec. 3.1.
- RRSIG go.id/DNSKEY alg 10, id 48051: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 10 (RSASHA512). See RFC 8624, Sec. 3.1.
- RRSIG go.id/DNSKEY alg 10, id 48051: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 10 (RSASHA512). See RFC 8624, Sec. 3.1.
- RRSIG go.id/SOA alg 10, id 25427: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 10 (RSASHA512). See RFC 8624, Sec. 3.1.
- go.id/DS (alg 10, id 48051): No response was received from the server over UDP (tried 7 times) until the NSID EDNS option was removed (however, this server appeared to respond legitimately to other queries with the NSID EDNS option present). See RFC 6891, Sec. 6.1.2. (2001:df5:4000:4::4, UDP_-_EDNS0_4096_D_KN)
- go.id/DS (alg 10, id 48051): No response was received from the server over UDP (tried 7 times) until the NSID EDNS option was removed (however, this server appeared to respond legitimately to other queries with the NSID EDNS option present). See RFC 6891, Sec. 6.1.2. (2001:df5:4000:4::4, UDP_-_EDNS0_4096_D_KN)
- go.id/DS (alg 10, id 48051): No response was received until the UDP payload size was decreased, indicating that the server might be attempting to send a payload that exceeds the path maximum transmission unit (PMTU) size. See RFC 6891, Sec. 6.2.6. (103.19.177.177, UDP_-_EDNS0_4096_D_KN)
- go.id/DS (alg 10, id 48051): No response was received until the UDP payload size was decreased, indicating that the server might be attempting to send a payload that exceeds the path maximum transmission unit (PMTU) size. See RFC 6891, Sec. 6.2.6. (103.19.177.177, UDP_-_EDNS0_4096_D_KN)
- polkam.go.id/DS has warnings; select the "Denial of existence" DNSSEC option to see them.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.