nethuis.nl
Updated:
2021-05-05 14:05:39 UTC (1290 days ago)
Go to most recent »
Notices
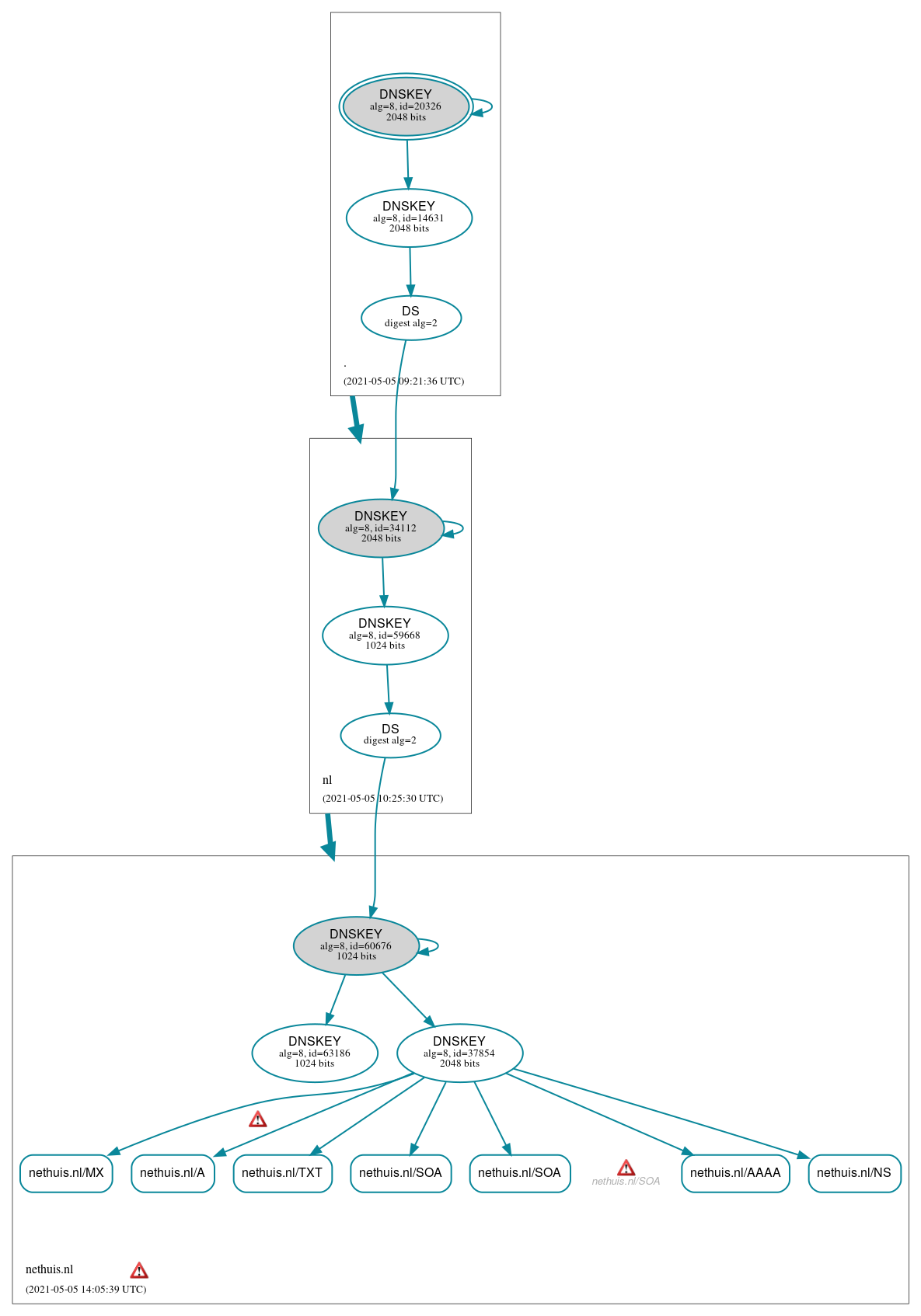
DNSSEC Authentication Chain
 RRset status
RRset status
Secure (7)
- nethuis.nl/A
- nethuis.nl/AAAA
- nethuis.nl/MX
- nethuis.nl/NS
- nethuis.nl/SOA
- nethuis.nl/SOA
- nethuis.nl/TXT
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (9)
- ./DNSKEY (alg 8, id 14631)
- ./DNSKEY (alg 8, id 20326)
- nethuis.nl/DNSKEY (alg 8, id 37854)
- nethuis.nl/DNSKEY (alg 8, id 60676)
- nethuis.nl/DNSKEY (alg 8, id 63186)
- nethuis.nl/DS (alg 8, id 60676)
- nl/DNSKEY (alg 8, id 34112)
- nl/DNSKEY (alg 8, id 59668)
- nl/DS (alg 8, id 34112)
 Delegation status
Delegation status
Secure (2)
- . to nl
- nl to nethuis.nl
 Notices
Notices
Errors (4)
- RRSIG nethuis.nl/MX alg 8, id 37854: With a TTL of 2419200 the RRSIG RR can be in the cache of a non-validating resolver until 20 days after it expires at 2021-05-13 00:00:00+00:00. See RFC 4035, Sec. 5.3.3.
- nethuis.nl zone: The server(s) were not responsive to queries over TCP. See RFC 1035, Sec. 4.2. (195.8.195.195, 2a01:7c8:f:c1f::195)
- nethuis.nl/SOA: No response was received from the server over TCP (tried 3 times). See RFC 1035, Sec. 4.2. (2a01:7c8:f:c1f::195, TCP_-_EDNS0_4096_D_N)
- nethuis.nl/SOA: No response was received from the server over TCP (tried 5 times). See RFC 1035, Sec. 4.2. (195.8.195.195, TCP_-_EDNS0_4096_D_N)





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.