netcool.org
Updated:
2022-09-18 17:07:32 UTC (827 days ago)
Go to most recent »
Notices
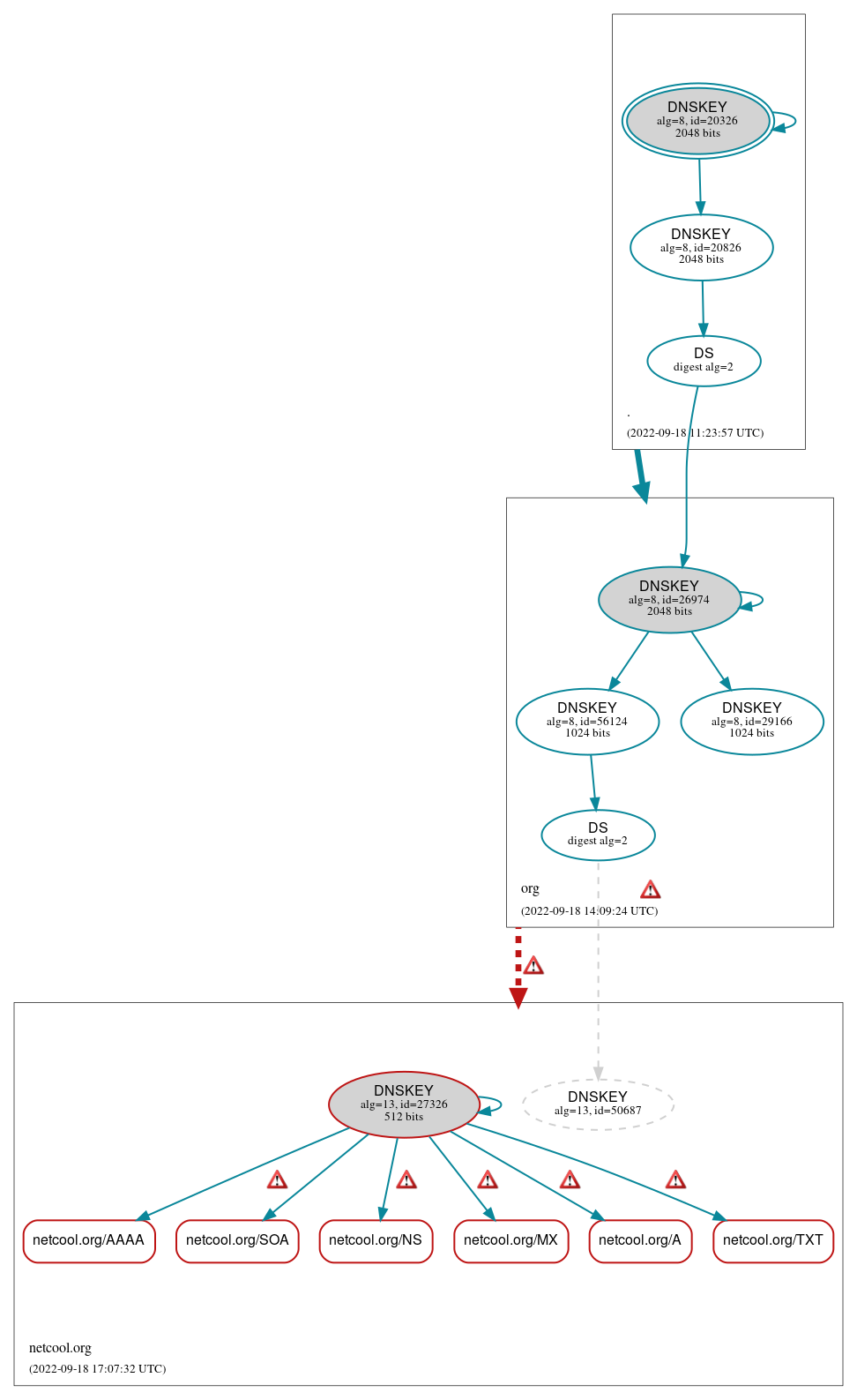
DNSSEC Authentication Chain
 RRset status
RRset status
Bogus (6)
- netcool.org/A
- netcool.org/AAAA
- netcool.org/MX
- netcool.org/NS
- netcool.org/SOA
- netcool.org/TXT
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Bogus (1)
- netcool.org/DNSKEY (alg 13, id 27326)
Secure (7)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 20826)
- netcool.org/DS (alg 13, id 50687)
- org/DNSKEY (alg 8, id 26974)
- org/DNSKEY (alg 8, id 29166)
- org/DNSKEY (alg 8, id 56124)
- org/DS (alg 8, id 26974)
Non_existent (1)
- netcool.org/DNSKEY (alg 13, id 50687)
 Delegation status
Delegation status
Bogus (1)
- org to netcool.org
Secure (1)
- . to org
 Notices
Notices
Errors (8)
- RRSIG netcool.org/A alg 13, id 27326: With a TTL of 604800 the RRSIG RR can be in the cache of a non-validating resolver until 14 hours, 50 minutes after it expires at 2022-09-25 02:16:55+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG netcool.org/AAAA alg 13, id 27326: With a TTL of 604800 the RRSIG RR can be in the cache of a non-validating resolver until 14 hours, 50 minutes after it expires at 2022-09-25 02:16:55+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG netcool.org/MX alg 13, id 27326: With a TTL of 604800 the RRSIG RR can be in the cache of a non-validating resolver until 14 hours, 50 minutes after it expires at 2022-09-25 02:16:55+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG netcool.org/NS alg 13, id 27326: With a TTL of 604800 the RRSIG RR can be in the cache of a non-validating resolver until 14 hours, 50 minutes after it expires at 2022-09-25 02:16:55+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG netcool.org/TXT alg 13, id 27326: With a TTL of 604800 the RRSIG RR can be in the cache of a non-validating resolver until 14 hours, 50 minutes after it expires at 2022-09-25 02:16:55+00:00. See RFC 4035, Sec. 5.3.3.
- org to netcool.org: No valid RRSIGs made by a key corresponding to a DS RR were found covering the DNSKEY RRset, resulting in no secure entry point (SEP) into the zone. See RFC 4035, Sec. 2.2, RFC 6840, Sec. 5.11. (45.32.139.108, 45.32.139.177, 192.249.57.242, 192.249.57.243, 207.148.19.107, 207.246.89.140, 2001:19f0:5:275::ba, 2001:19f0:5:275::bb, 2001:19f0:ac01:1692::ca, 2001:19f0:ac01:1692::cb, 2604:180:0:239::aa, 2604:180:0:239::ab, UDP_-_EDNS0_4096_D_KN, UDP_-_EDNS0_512_D_KN)
- org to netcool.org: The DS RRset for the zone included algorithm 13 (ECDSAP256SHA256), but no DS RR matched a DNSKEY with algorithm 13 that signs the zone's DNSKEY RRset. See RFC 4035, Sec. 2.2, RFC 6840, Sec. 5.11. (45.32.139.108, 45.32.139.177, 192.249.57.242, 192.249.57.243, 207.148.19.107, 207.246.89.140, 2001:19f0:5:275::ba, 2001:19f0:5:275::bb, 2001:19f0:ac01:1692::ca, 2001:19f0:ac01:1692::cb, 2604:180:0:239::aa, 2604:180:0:239::ab, UDP_-_EDNS0_4096_D_KN, UDP_-_EDNS0_512_D_KN)
- org zone: The server(s) were not responsive to queries over UDP. See RFC 1035, Sec. 4.2. (2001:500:c::1)





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.