monmouth.edu
Updated:
2020-09-21 15:16:04 UTC (1525 days ago)
Go to most recent »
Notices
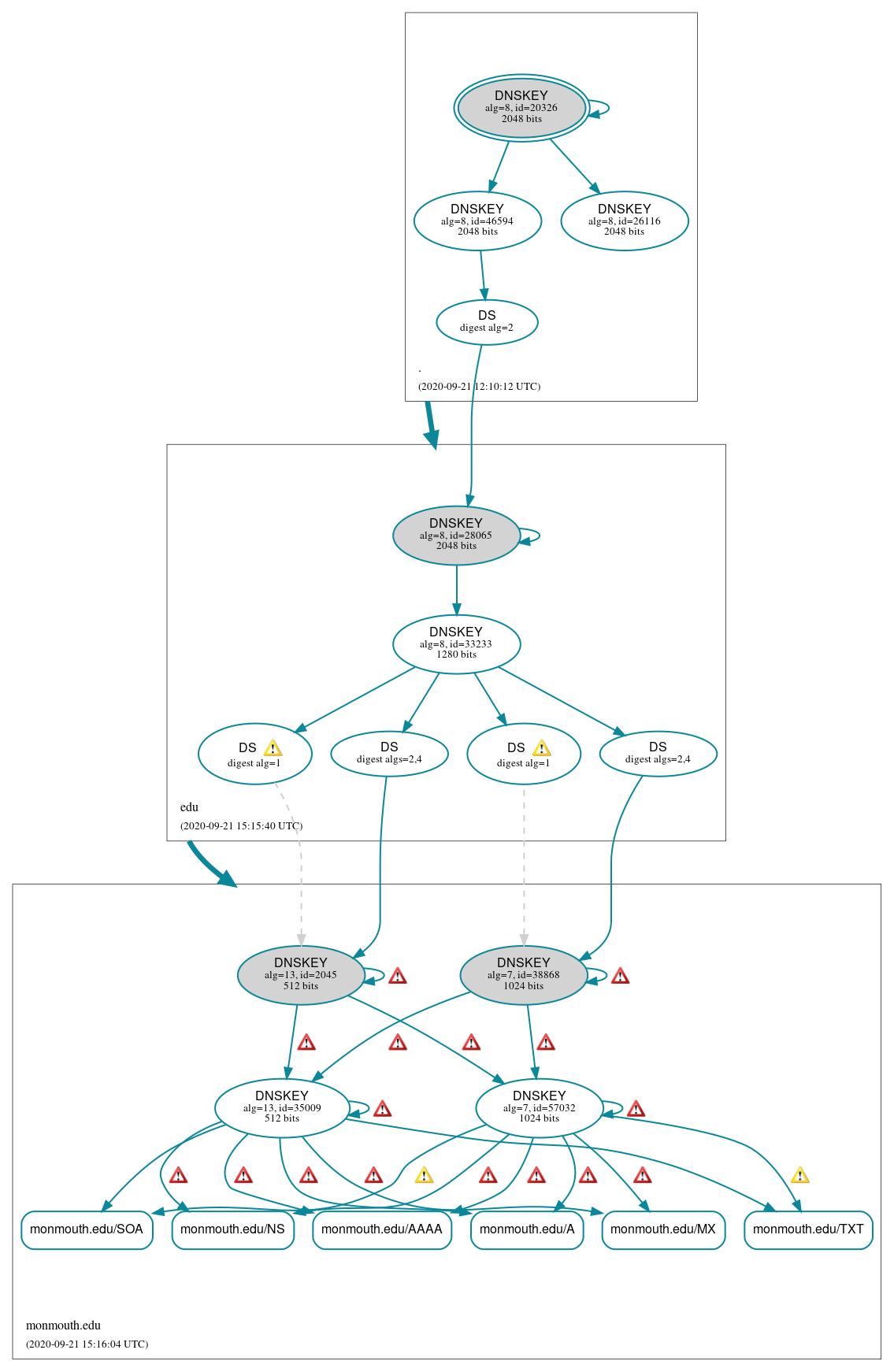
DNSSEC Authentication Chain
 RRset status
RRset status
Secure (6)
- monmouth.edu/A
- monmouth.edu/AAAA
- monmouth.edu/MX
- monmouth.edu/NS
- monmouth.edu/SOA
- monmouth.edu/TXT
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (14)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 26116)
- ./DNSKEY (alg 8, id 46594)
- edu/DNSKEY (alg 8, id 28065)
- edu/DNSKEY (alg 8, id 33233)
- edu/DS (alg 8, id 28065)
- monmouth.edu/DNSKEY (alg 13, id 2045)
- monmouth.edu/DNSKEY (alg 13, id 35009)
- monmouth.edu/DNSKEY (alg 7, id 38868)
- monmouth.edu/DNSKEY (alg 7, id 57032)
- monmouth.edu/DS (alg 13, id 2045)
- monmouth.edu/DS (alg 13, id 2045)
- monmouth.edu/DS (alg 7, id 38868)
- monmouth.edu/DS (alg 7, id 38868)
 Delegation status
Delegation status
Secure (2)
- . to edu
- edu to monmouth.edu
 Notices
Notices
Errors (27)
- RRSIG monmouth.edu/A alg 13, id 35009: With a TTL of 3600 the RRSIG RR can be in the cache of a non-validating resolver until 52 minutes after it expires at 2020-09-21 15:23:20+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/A alg 7, id 57032: With a TTL of 3600 the RRSIG RR can be in the cache of a non-validating resolver until 52 minutes after it expires at 2020-09-21 15:23:20+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/AAAA alg 13, id 35009: With a TTL of 3600 the RRSIG RR can be in the cache of a non-validating resolver until 29 minutes after it expires at 2020-09-21 15:46:41+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/AAAA alg 7, id 57032: With a TTL of 3600 the RRSIG RR can be in the cache of a non-validating resolver until 29 minutes after it expires at 2020-09-21 15:46:41+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 13, id 2045: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 13, id 2045: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 13, id 2045: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 13, id 2045: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 13, id 35009: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 13, id 35009: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 13, id 35009: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 13, id 35009: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 7, id 38868: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 7, id 38868: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 7, id 38868: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 7, id 38868: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 7, id 57032: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 7, id 57032: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 7, id 57032: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/DNSKEY alg 7, id 57032: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 38 minutes after it expires at 2020-09-21 15:38:02+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/MX alg 13, id 35009: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 52 minutes after it expires at 2020-09-21 15:23:20+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/MX alg 7, id 57032: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 52 minutes after it expires at 2020-09-21 15:23:20+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/NS alg 13, id 35009: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 29 minutes after it expires at 2020-09-21 15:46:41+00:00. See RFC 4035, Sec. 5.3.3.
- RRSIG monmouth.edu/NS alg 7, id 57032: With a TTL of 86400 the RRSIG RR can be in the cache of a non-validating resolver until 23 hours, 29 minutes after it expires at 2020-09-21 15:46:41+00:00. See RFC 4035, Sec. 5.3.3.
- i75huts4cq.monmouth.edu/A has errors; select the "Denial of existence" DNSSEC option to see them.
- monmouth.edu/DNSKEY has errors; select the "Denial of existence" DNSSEC option to see them.
- monmouth.edu/CNAME has errors; select the "Denial of existence" DNSSEC option to see them.
Warnings (29)
- RRSIG monmouth.edu/A alg 7, id 57032: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 7 (RSASHA1NSEC3SHA1). See RFC 8624, Sec. 3.1.
- RRSIG monmouth.edu/AAAA alg 7, id 57032: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 7 (RSASHA1NSEC3SHA1). See RFC 8624, Sec. 3.1.
- RRSIG monmouth.edu/DNSKEY alg 7, id 38868: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 7 (RSASHA1NSEC3SHA1). See RFC 8624, Sec. 3.1.
- RRSIG monmouth.edu/DNSKEY alg 7, id 38868: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 7 (RSASHA1NSEC3SHA1). See RFC 8624, Sec. 3.1.
- RRSIG monmouth.edu/DNSKEY alg 7, id 38868: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 7 (RSASHA1NSEC3SHA1). See RFC 8624, Sec. 3.1.
- RRSIG monmouth.edu/DNSKEY alg 7, id 38868: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 7 (RSASHA1NSEC3SHA1). See RFC 8624, Sec. 3.1.
- RRSIG monmouth.edu/DNSKEY alg 7, id 57032: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 7 (RSASHA1NSEC3SHA1). See RFC 8624, Sec. 3.1.
- RRSIG monmouth.edu/DNSKEY alg 7, id 57032: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 7 (RSASHA1NSEC3SHA1). See RFC 8624, Sec. 3.1.
- RRSIG monmouth.edu/DNSKEY alg 7, id 57032: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 7 (RSASHA1NSEC3SHA1). See RFC 8624, Sec. 3.1.
- RRSIG monmouth.edu/DNSKEY alg 7, id 57032: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 7 (RSASHA1NSEC3SHA1). See RFC 8624, Sec. 3.1.
- RRSIG monmouth.edu/MX alg 7, id 57032: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 7 (RSASHA1NSEC3SHA1). See RFC 8624, Sec. 3.1.
- RRSIG monmouth.edu/NS alg 7, id 57032: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 7 (RSASHA1NSEC3SHA1). See RFC 8624, Sec. 3.1.
- RRSIG monmouth.edu/SOA alg 7, id 57032: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 7 (RSASHA1NSEC3SHA1). See RFC 8624, Sec. 3.1.
- RRSIG monmouth.edu/TXT alg 7, id 57032: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 7 (RSASHA1NSEC3SHA1). See RFC 8624, Sec. 3.1.
- monmouth.edu/DS (alg 13, id 2045): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- monmouth.edu/DS (alg 13, id 2045): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- monmouth.edu/DS (alg 13, id 2045): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- monmouth.edu/DS (alg 13, id 2045): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- monmouth.edu/DS (alg 13, id 2045): In the spirit of RFC 4509, DS records with digest type 1 (SHA-1) might be ignored when DS records with digest type 4 (SHA-384) exist in the same RRset. See RFC 4509, Sec. 3.
- monmouth.edu/DS (alg 13, id 2045): In the spirit of RFC 4509, DS records with digest type 1 (SHA-1) might be ignored when DS records with digest type 4 (SHA-384) exist in the same RRset. See RFC 4509, Sec. 3.
- monmouth.edu/DS (alg 7, id 38868): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- monmouth.edu/DS (alg 7, id 38868): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- monmouth.edu/DS (alg 7, id 38868): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- monmouth.edu/DS (alg 7, id 38868): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- monmouth.edu/DS (alg 7, id 38868): In the spirit of RFC 4509, DS records with digest type 1 (SHA-1) might be ignored when DS records with digest type 4 (SHA-384) exist in the same RRset. See RFC 4509, Sec. 3.
- monmouth.edu/DS (alg 7, id 38868): In the spirit of RFC 4509, DS records with digest type 1 (SHA-1) might be ignored when DS records with digest type 4 (SHA-384) exist in the same RRset. See RFC 4509, Sec. 3.
- i75huts4cq.monmouth.edu/A has warnings; select the "Denial of existence" DNSSEC option to see them.
- monmouth.edu/DNSKEY has warnings; select the "Denial of existence" DNSSEC option to see them.
- monmouth.edu/CNAME has warnings; select the "Denial of existence" DNSSEC option to see them.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.