kth.se
Updated:
2020-04-12 08:08:13 UTC (1688 days ago)
Go to most recent »
Notices
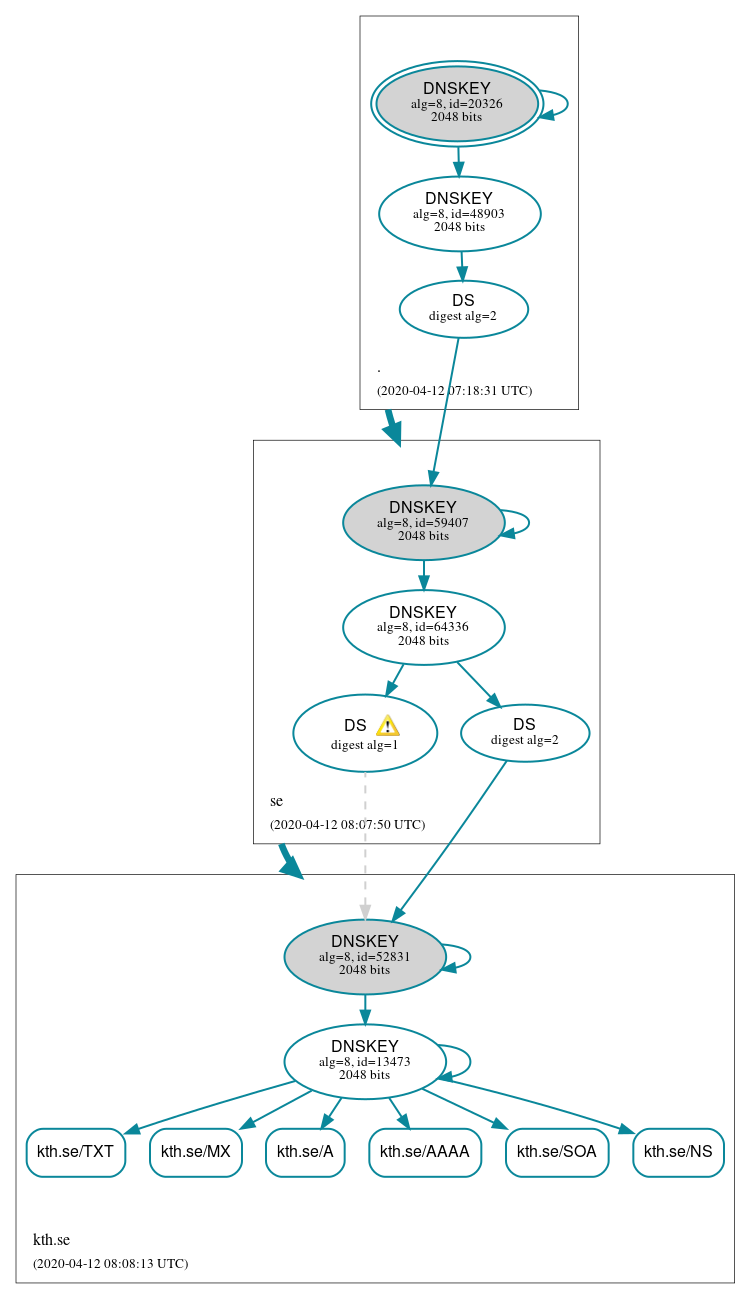
DNSSEC Authentication Chain
 RRset status
RRset status
Secure (6)
- kth.se/A
- kth.se/AAAA
- kth.se/MX
- kth.se/NS
- kth.se/SOA
- kth.se/TXT
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (9)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 48903)
- kth.se/DNSKEY (alg 8, id 13473)
- kth.se/DNSKEY (alg 8, id 52831)
- kth.se/DS (alg 8, id 52831)
- kth.se/DS (alg 8, id 52831)
- se/DNSKEY (alg 8, id 59407)
- se/DNSKEY (alg 8, id 64336)
- se/DS (alg 8, id 59407)
 Delegation status
Delegation status
Secure (2)
- . to se
- se to kth.se
 Notices
Notices
Warnings (4)
- kth.se/DS (alg 8, id 52831): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- kth.se/DS (alg 8, id 52831): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- kth.se/DS (alg 8, id 52831): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- kth.se/DS (alg 8, id 52831): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.