kenic.or.ke
Updated:
2021-10-08 06:31:32 UTC (1136 days ago)
Go to most recent »
Notices
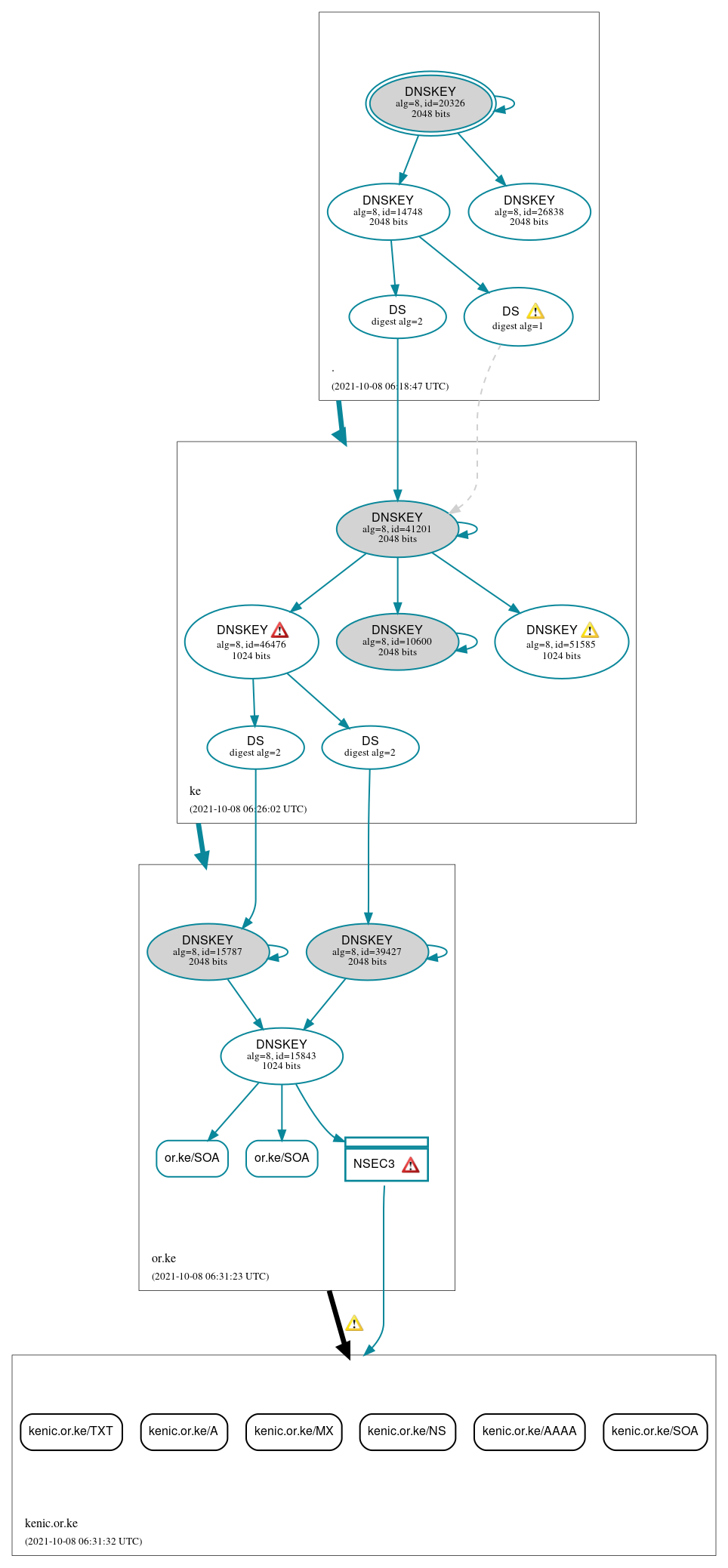
DNSSEC Authentication Chain
 RRset status
RRset status
Insecure (6)
- kenic.or.ke/A
- kenic.or.ke/AAAA
- kenic.or.ke/MX
- kenic.or.ke/NS
- kenic.or.ke/SOA
- kenic.or.ke/TXT
Secure (2)
- or.ke/SOA
- or.ke/SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (15)
- ./DNSKEY (alg 8, id 14748)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 26838)
- NSEC3 proving non-existence of kenic.or.ke/DS
- ke/DNSKEY (alg 8, id 10600)
- ke/DNSKEY (alg 8, id 41201)
- ke/DNSKEY (alg 8, id 46476)
- ke/DNSKEY (alg 8, id 51585)
- ke/DS (alg 8, id 41201)
- ke/DS (alg 8, id 41201)
- or.ke/DNSKEY (alg 8, id 15787)
- or.ke/DNSKEY (alg 8, id 15843)
- or.ke/DNSKEY (alg 8, id 39427)
- or.ke/DS (alg 8, id 15787)
- or.ke/DS (alg 8, id 39427)
 Delegation status
Delegation status
Insecure (1)
- or.ke to kenic.or.ke
Secure (2)
- . to ke
- ke to or.ke
 Notices
Notices
Errors (4)
- NSEC3 proving non-existence of kenic.or.ke/DS: An iterations count of 0 must be used in NSEC3 records to alleviate computational burdens. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of kenic.or.ke/DS: An iterations count of 0 must be used in NSEC3 records to alleviate computational burdens. See RFC 9276, Sec. 3.1.
- ke/DNSKEY (alg 8, id 46476): The DNSKEY RR was not found in the DNSKEY RRset returned by one or more servers. (147.135.106.237, 196.1.4.3, 196.1.4.130, 196.216.168.22, 198.32.67.9, 204.61.216.7, 2001:500:14:6007:ad::1, 2001:43f8:10:0:50c0:a8ff:feee:30, 2001:43f8:120::22, 2604:2dc0:200:2eb::237, TCP_-_EDNS0_4096_D_KN, UDP_-_EDNS0_4096_D_KN)
- kenic.or.ke/DS has errors; select the "Denial of existence" DNSSEC option to see them.
Warnings (9)
- NSEC3 proving non-existence of kenic.or.ke/DS: The salt value for an NSEC3 record should be empty. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of kenic.or.ke/DS: The salt value for an NSEC3 record should be empty. See RFC 9276, Sec. 3.1.
- ke/DNSKEY (alg 8, id 51585): The DNSKEY RR was not found in the DNSKEY RRset returned by one or more servers. (185.28.194.194, 185.38.108.108, UDP_-_EDNS0_4096_D_KN)
- ke/DS (alg 8, id 41201): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- ke/DS (alg 8, id 41201): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- ke/DS (alg 8, id 41201): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- ke/DS (alg 8, id 41201): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- or.ke to kenic.or.ke: Authoritative AAAA records exist for ns.anycast.kenic.or.ke, but there are no corresponding AAAA glue records. See RFC 1034, Sec. 4.2.2.
- kenic.or.ke/DS has warnings; select the "Denial of existence" DNSSEC option to see them.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.