health.mil
Updated:
2024-10-17 13:24:11 UTC (419 days ago)
Go to most recent »
Notices
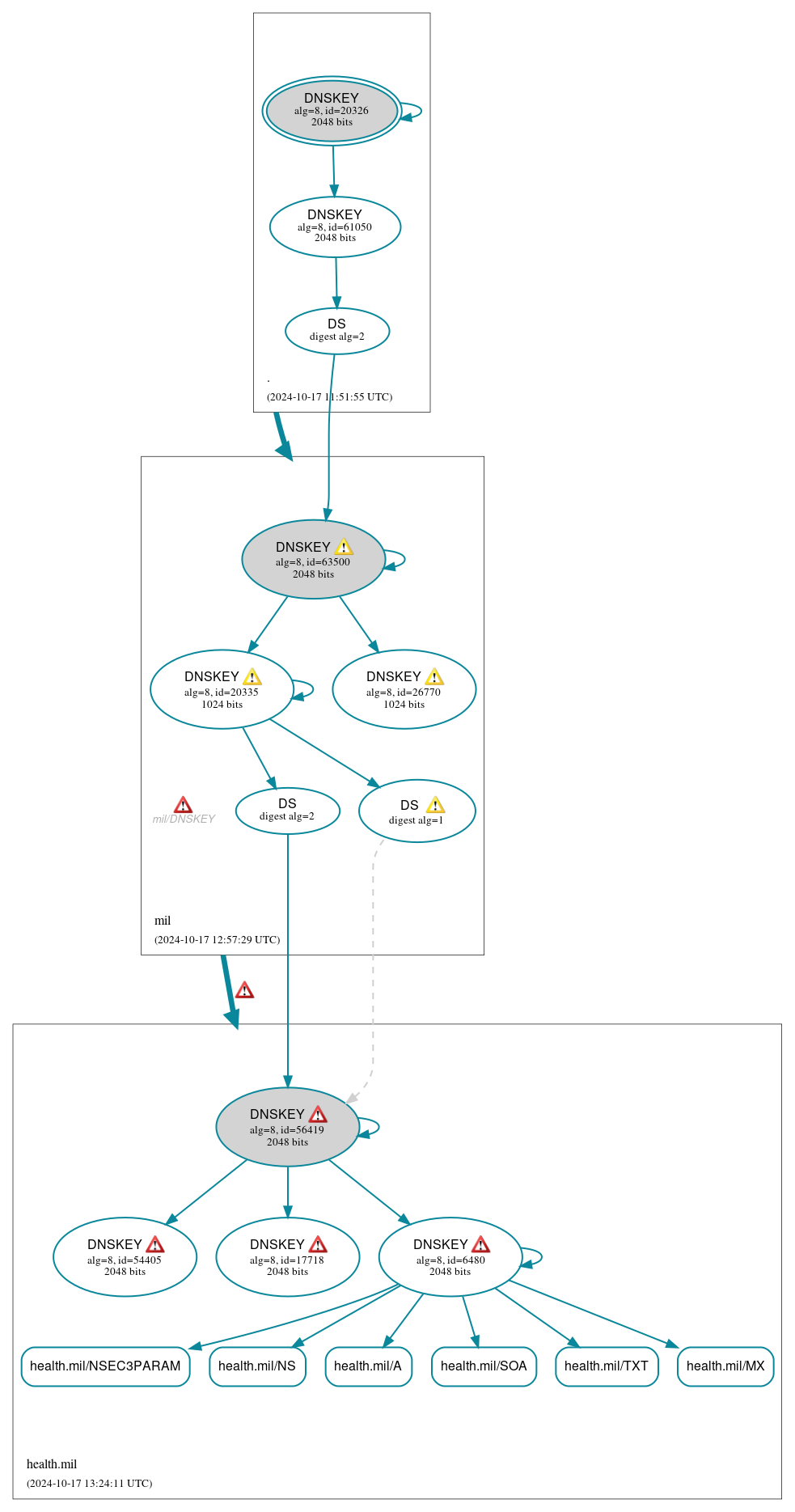
DNSSEC Authentication Chain
 RRset status
RRset status
Secure (6)
- health.mil/A
- health.mil/MX
- health.mil/NS
- health.mil/NSEC3PARAM
- health.mil/SOA
- health.mil/TXT
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (12)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 61050)
- health.mil/DNSKEY (alg 8, id 17718)
- health.mil/DNSKEY (alg 8, id 54405)
- health.mil/DNSKEY (alg 8, id 56419)
- health.mil/DNSKEY (alg 8, id 6480)
- health.mil/DS (alg 8, id 56419)
- health.mil/DS (alg 8, id 56419)
- mil/DNSKEY (alg 8, id 20335)
- mil/DNSKEY (alg 8, id 26770)
- mil/DNSKEY (alg 8, id 63500)
- mil/DS (alg 8, id 63500)
 Delegation status
Delegation status
Secure (2)
- . to mil
- mil to health.mil
 Notices
Notices
Errors (13)
- health.mil/DNSKEY (alg 8, id 17718): No RRSIG covering the RRset was returned in the response. See RFC 4035, Sec. 3.1.1. (214.2.208.178, 214.2.212.178, UDP_-_EDNS0_4096_D_KN)
- health.mil/DNSKEY (alg 8, id 54405): No RRSIG covering the RRset was returned in the response. See RFC 4035, Sec. 3.1.1. (214.2.208.178, 214.2.212.178, UDP_-_EDNS0_4096_D_KN)
- health.mil/DNSKEY (alg 8, id 56419): No RRSIG covering the RRset was returned in the response. See RFC 4035, Sec. 3.1.1. (214.2.208.178, 214.2.212.178, UDP_-_EDNS0_4096_D_KN)
- health.mil/DNSKEY (alg 8, id 6480): No RRSIG covering the RRset was returned in the response. See RFC 4035, Sec. 3.1.1. (214.2.208.178, 214.2.212.178, UDP_-_EDNS0_4096_D_KN)
- mil to health.mil: No valid RRSIGs made by a key corresponding to a DS RR were found covering the DNSKEY RRset, resulting in no secure entry point (SEP) into the zone. See RFC 4035, Sec. 2.2, RFC 6840, Sec. 5.11. (214.2.208.178, 214.2.212.178, UDP_-_EDNS0_4096_D_KN)
- mil to health.mil: The DS RRset for the zone included algorithm 8 (RSASHA256), but no DS RR matched a DNSKEY with algorithm 8 that signs the zone's DNSKEY RRset. See RFC 4035, Sec. 2.2, RFC 6840, Sec. 5.11. (214.2.208.178, 214.2.212.178, UDP_-_EDNS0_4096_D_KN)
- mil/DNSKEY: No response was received from the server over UDP (tried 4 times). See RFC 1035, Sec. 4.2. (199.252.155.234, UDP_-_EDNS0_512_D_KN)
- health.mil/CDNSKEY has errors; select the "Denial of existence" DNSSEC option to see them.
- health.mil/AAAA has errors; select the "Denial of existence" DNSSEC option to see them.
- health.mil/CDS has errors; select the "Denial of existence" DNSSEC option to see them.
- health.mil/DNSKEY has errors; select the "Denial of existence" DNSSEC option to see them.
- health.mil/CNAME has errors; select the "Denial of existence" DNSSEC option to see them.
- gvr5m.nsv0x.health.mil/A has errors; select the "Denial of existence" DNSSEC option to see them.
Warnings (13)
- health.mil/DS (alg 8, id 56419): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- health.mil/DS (alg 8, id 56419): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- health.mil/DS (alg 8, id 56419): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- health.mil/DS (alg 8, id 56419): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- mil to health.mil: The following NS name(s) were found in the authoritative NS RRset, but not in the delegation NS RRset (i.e., in the mil zone): ns01-swc-gw.health.mil See RFC 1034, Sec. 4.2.2.
- mil/DNSKEY (alg 8, id 20335): No response was received until the UDP payload size was decreased, indicating that the server might be attempting to send a payload that exceeds the path maximum transmission unit (PMTU) size. See RFC 6891, Sec. 6.2.6. (199.252.155.234, UDP_-_EDNS0_4096_D_KN)
- mil/DNSKEY (alg 8, id 26770): No response was received until the UDP payload size was decreased, indicating that the server might be attempting to send a payload that exceeds the path maximum transmission unit (PMTU) size. See RFC 6891, Sec. 6.2.6. (199.252.155.234, UDP_-_EDNS0_4096_D_KN)
- mil/DNSKEY (alg 8, id 63500): No response was received until the UDP payload size was decreased, indicating that the server might be attempting to send a payload that exceeds the path maximum transmission unit (PMTU) size. See RFC 6891, Sec. 6.2.6. (199.252.155.234, UDP_-_EDNS0_4096_D_KN)
- health.mil/CDS has warnings; select the "Denial of existence" DNSSEC option to see them.
- health.mil/CDNSKEY has warnings; select the "Denial of existence" DNSSEC option to see them.
- health.mil/CNAME has warnings; select the "Denial of existence" DNSSEC option to see them.
- gvr5m.nsv0x.health.mil/A has warnings; select the "Denial of existence" DNSSEC option to see them.
- health.mil/AAAA has warnings; select the "Denial of existence" DNSSEC option to see them.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.