gov.tr
Updated:
2023-04-02 17:19:14 UTC (536 days ago)
Go to most recent »
Notices
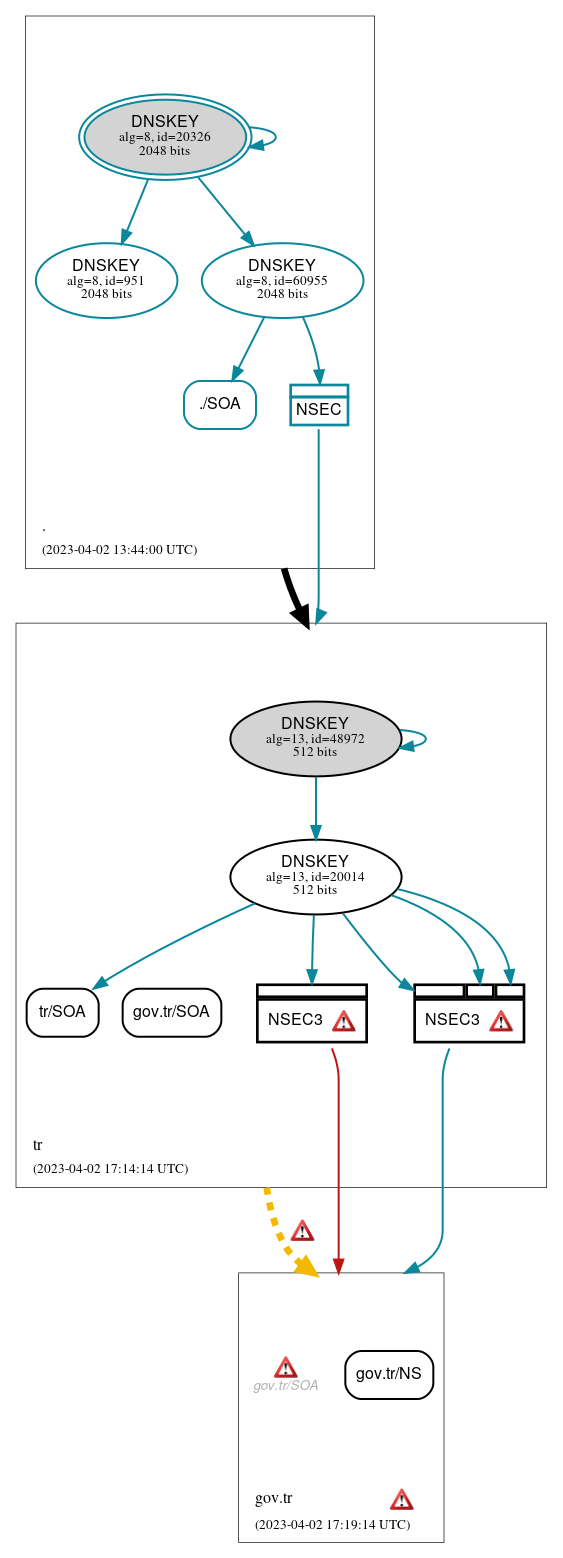
DNSSEC Authentication Chain
 RRset status
RRset status
Insecure (3)
- gov.tr/NS
- gov.tr/SOA
- tr/SOA
Secure (1)
- ./SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Insecure (4)
- NSEC3 proving non-existence of gov.tr/DS
- NSEC3 proving non-existence of gov.tr/DS
- tr/DNSKEY (alg 13, id 20014)
- tr/DNSKEY (alg 13, id 48972)
Secure (4)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 60955)
- ./DNSKEY (alg 8, id 951)
- NSEC proving non-existence of tr/DS
 Delegation status
Delegation status
Incomplete (1)
- tr to gov.tr
Insecure (1)
- . to tr
 Notices
Notices
Errors (12)
- NSEC3 proving non-existence of gov.tr/DS: An iterations count of 0 must be used in NSEC3 records to alleviate computational burdens. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of gov.tr/DS: An iterations count of 0 must be used in NSEC3 records to alleviate computational burdens. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of gov.tr/DS: An iterations count of 0 must be used in NSEC3 records to alleviate computational burdens. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of gov.tr/DS: An iterations count of 0 must be used in NSEC3 records to alleviate computational burdens. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of gov.tr/DS: No NSEC3 RR matches the SNAME (gov.tr). See RFC 5155, Sec. 8.6.
- NSEC3 proving non-existence of gov.tr/DS: No NSEC3 RR matches the SNAME (gov.tr). See RFC 5155, Sec. 8.6.
- gov.tr zone: The server(s) were not responsive to queries over TCP. See RFC 1035, Sec. 4.2. (31.145.139.119, 2001:a98:10:eeee::42)
- gov.tr/SOA: No response was received from the server over TCP (tried 3 times). See RFC 1035, Sec. 4.2. (31.145.139.119, 2001:a98:10:eeee::42, TCP_-_EDNS0_4096_D_N)
- tr to gov.tr: An SOA RR with owner name (gov.tr) not matching the zone name (tr) was returned with the NODATA response. See RFC 1034, Sec. 4.3.4, RFC 2308, Sec. 2.2. (31.145.139.99, 31.145.139.119, 185.7.0.2, 185.7.0.3, 2001:a98:10:eeee::41, 2001:a98:10:eeee::42, UDP_-_EDNS0_4096_D_KN)
- tr to gov.tr: No NSEC RR(s) were returned to validate the NODATA response. See RFC 4035, Sec. 3.1.3.1, RFC 5155, Sec. 7.2.3, RFC 5155, Sec. 7.2.4. (31.145.139.99, 31.145.139.119, 185.7.0.2, 185.7.0.3, 2001:a98:10:eeee::41, 2001:a98:10:eeee::42, UDP_-_EDNS0_4096_D_KN)
- tr to gov.tr: No delegation NS records were detected in the parent zone (tr). This results in an NXDOMAIN response to a DS query (for DNSSEC), even if the parent servers are authoritative for the child. See RFC 1034, Sec. 4.2.2. (206.51.254.1, 2620:171:804:ad2::1, UDP_-_EDNS0_4096_D_KN)
- gov.tr/DS has errors; select the "Denial of existence" DNSSEC option to see them.
Warnings (5)
- NSEC3 proving non-existence of gov.tr/DS: The salt value for an NSEC3 record should be empty. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of gov.tr/DS: The salt value for an NSEC3 record should be empty. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of gov.tr/DS: The salt value for an NSEC3 record should be empty. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of gov.tr/DS: The salt value for an NSEC3 record should be empty. See RFC 9276, Sec. 3.1.
- gov.tr/DS has warnings; select the "Denial of existence" DNSSEC option to see them.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.