gov.au
Updated:
2023-06-09 01:33:08 UTC (583 days ago)
Go to most recent »
Notices
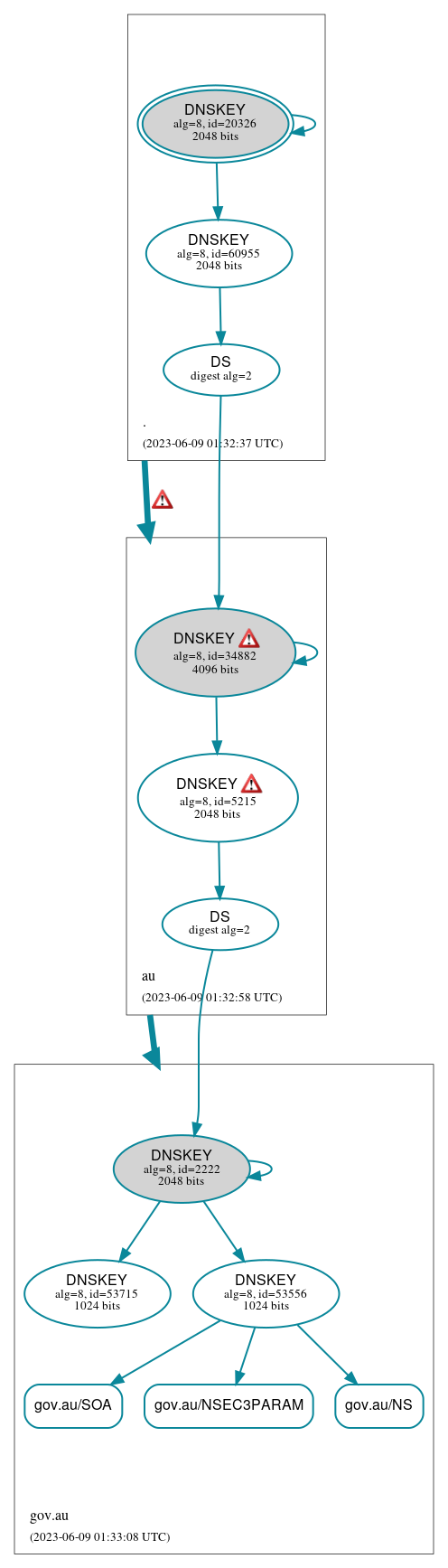
DNSSEC Authentication Chain
 RRset status
RRset status
Secure (3)
- gov.au/NS
- gov.au/NSEC3PARAM
- gov.au/SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (9)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 60955)
- au/DNSKEY (alg 8, id 34882)
- au/DNSKEY (alg 8, id 5215)
- au/DS (alg 8, id 34882)
- gov.au/DNSKEY (alg 8, id 2222)
- gov.au/DNSKEY (alg 8, id 53556)
- gov.au/DNSKEY (alg 8, id 53715)
- gov.au/DS (alg 8, id 2222)
 Delegation status
Delegation status
Secure (2)
- . to au
- au to gov.au
 Notices
Notices
Errors (12)
- . to au: No valid RRSIGs made by a key corresponding to a DS RR were found covering the DNSKEY RRset, resulting in no secure entry point (SEP) into the zone. See RFC 4035, Sec. 2.2, RFC 6840, Sec. 5.11. (2400:cb00:2049:1::a29f:1926, TCP_-_NOEDNS_)
- . to au: The DS RRset for the zone included algorithm 8 (RSASHA256), but no DS RR matched a DNSKEY with algorithm 8 that signs the zone's DNSKEY RRset. See RFC 4035, Sec. 2.2, RFC 6840, Sec. 5.11. (2400:cb00:2049:1::a29f:1926, TCP_-_NOEDNS_)
- au/DNSKEY (alg 8, id 34882): DNSSEC was effectively downgraded because the response had an invalid RCODE (SERVFAIL) with EDNS enabled. See RFC 6891, Sec. 7, RFC 2671, Sec. 5.3. (2400:cb00:2049:1::a29f:1926, TCP_-_NOEDNS_)
- au/DNSKEY (alg 8, id 34882): The response had an invalid RCODE (SERVFAIL) until EDNS was disabled (however, this server appeared to respond legitimately to other queries with EDNS enabled). See RFC 6891, Sec. 6.2.6. (2400:cb00:2049:1::a29f:1926, UDP_-_EDNS0_4096_D_KN)
- au/DNSKEY (alg 8, id 5215): DNSSEC was effectively downgraded because the response had an invalid RCODE (SERVFAIL) with EDNS enabled. See RFC 6891, Sec. 7, RFC 2671, Sec. 5.3. (2400:cb00:2049:1::a29f:1926, TCP_-_NOEDNS_)
- au/DNSKEY (alg 8, id 5215): The response had an invalid RCODE (SERVFAIL) until EDNS was disabled (however, this server appeared to respond legitimately to other queries with EDNS enabled). See RFC 6891, Sec. 6.2.6. (2400:cb00:2049:1::a29f:1926, UDP_-_EDNS0_4096_D_KN)
- gov.au/MX has errors; select the "Denial of existence" DNSSEC option to see them.
- y162rq4pmu.gov.au/A has errors; select the "Denial of existence" DNSSEC option to see them.
- gov.au/CNAME has errors; select the "Denial of existence" DNSSEC option to see them.
- gov.au/TXT has errors; select the "Denial of existence" DNSSEC option to see them.
- gov.au/AAAA has errors; select the "Denial of existence" DNSSEC option to see them.
- gov.au/A has errors; select the "Denial of existence" DNSSEC option to see them.
Warnings (6)
- gov.au/MX has warnings; select the "Denial of existence" DNSSEC option to see them.
- y162rq4pmu.gov.au/A has warnings; select the "Denial of existence" DNSSEC option to see them.
- gov.au/CNAME has warnings; select the "Denial of existence" DNSSEC option to see them.
- gov.au/TXT has warnings; select the "Denial of existence" DNSSEC option to see them.
- gov.au/AAAA has warnings; select the "Denial of existence" DNSSEC option to see them.
- gov.au/A has warnings; select the "Denial of existence" DNSSEC option to see them.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.