gn
Updated:
2023-10-10 07:20:33 UTC (462 days ago)
Go to most recent »
Notices
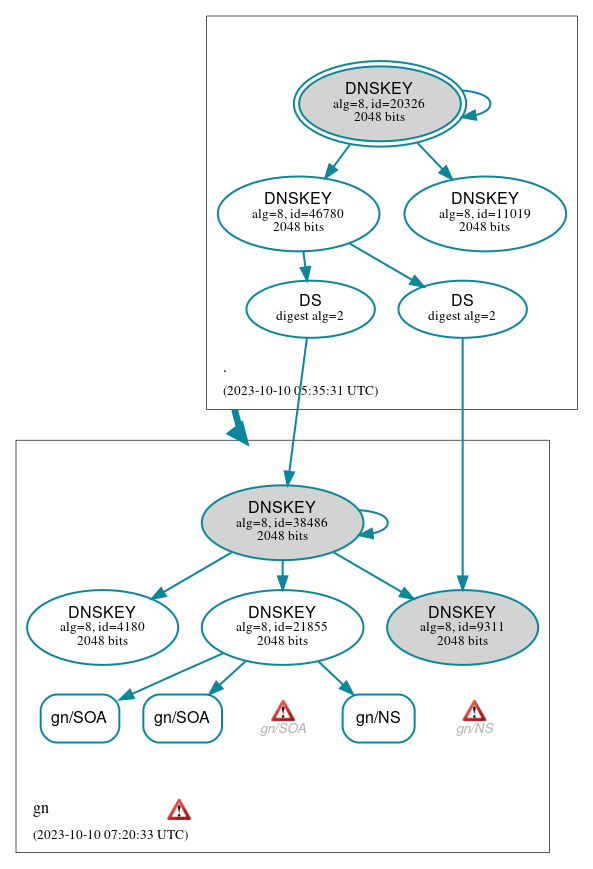
DNSSEC Authentication Chain
 RRset status
RRset status
Secure (3)
- gn/NS
- gn/SOA
- gn/SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (9)
- ./DNSKEY (alg 8, id 11019)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 46780)
- gn/DNSKEY (alg 8, id 21855)
- gn/DNSKEY (alg 8, id 38486)
- gn/DNSKEY (alg 8, id 4180)
- gn/DNSKEY (alg 8, id 9311)
- gn/DS (alg 8, id 38486)
- gn/DS (alg 8, id 9311)
 Delegation status
Delegation status
Secure (1)
- . to gn
 Notices
Notices
Errors (3)
- gn zone: The server(s) were not responsive to queries over UDP. See RFC 1035, Sec. 4.2. (196.216.168.49)
- gn/NS: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (196.216.168.49, UDP_-_NOEDNS_)
- gn/SOA: The TCP connection was interrupted (ECONNRESET). See RFC 1035, Sec. 4.2. (147.28.0.39, TCP_-_EDNS0_4096_D_N)





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.