fail02.dnssec.works
Updated:
2020-07-08 10:23:47 UTC (1628 days ago)
Go to most recent »
Notices
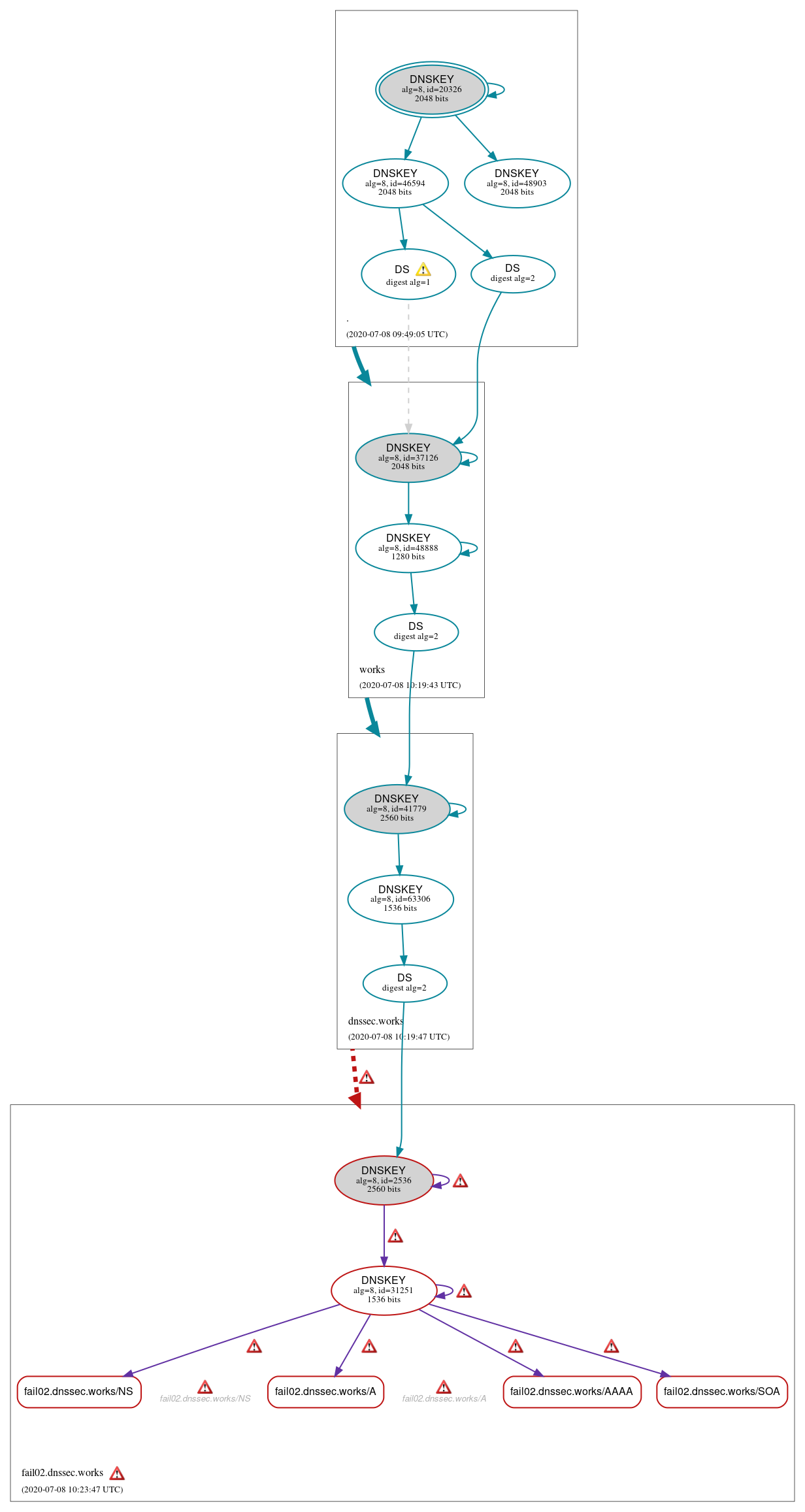
DNSSEC Authentication Chain
 RRset status
RRset status
Bogus (4)
- fail02.dnssec.works/A
- fail02.dnssec.works/AAAA
- fail02.dnssec.works/NS
- fail02.dnssec.works/SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Bogus (2)
- fail02.dnssec.works/DNSKEY (alg 8, id 2536)
- fail02.dnssec.works/DNSKEY (alg 8, id 31251)
Secure (11)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 46594)
- ./DNSKEY (alg 8, id 48903)
- dnssec.works/DNSKEY (alg 8, id 41779)
- dnssec.works/DNSKEY (alg 8, id 63306)
- dnssec.works/DS (alg 8, id 41779)
- fail02.dnssec.works/DS (alg 8, id 2536)
- works/DNSKEY (alg 8, id 37126)
- works/DNSKEY (alg 8, id 48888)
- works/DS (alg 8, id 37126)
- works/DS (alg 8, id 37126)
 Delegation status
Delegation status
Bogus (1)
- dnssec.works to fail02.dnssec.works
Secure (2)
- . to works
- works to dnssec.works
 Notices
Notices
Errors (17)
- RRSIG fail02.dnssec.works/A alg 8, id 31251: The Signature Expiration field of the RRSIG RR (1983-05-01 20:20:20+00:00) is 13582 days in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG fail02.dnssec.works/AAAA alg 8, id 31251: The Signature Expiration field of the RRSIG RR (1983-05-01 20:20:20+00:00) is 13582 days in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG fail02.dnssec.works/DNSKEY alg 8, id 2536: The Signature Expiration field of the RRSIG RR (1983-05-01 20:20:20+00:00) is 13582 days in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG fail02.dnssec.works/DNSKEY alg 8, id 2536: The Signature Expiration field of the RRSIG RR (1983-05-01 20:20:20+00:00) is 13582 days in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG fail02.dnssec.works/DNSKEY alg 8, id 31251: The Signature Expiration field of the RRSIG RR (1983-05-01 20:20:20+00:00) is 13582 days in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG fail02.dnssec.works/DNSKEY alg 8, id 31251: The Signature Expiration field of the RRSIG RR (1983-05-01 20:20:20+00:00) is 13582 days in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG fail02.dnssec.works/NS alg 8, id 31251: The Signature Expiration field of the RRSIG RR (1983-05-01 20:20:20+00:00) is 13582 days in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG fail02.dnssec.works/SOA alg 8, id 31251: The Signature Expiration field of the RRSIG RR (1983-05-01 20:20:20+00:00) is 13582 days in the past. See RFC 4035, Sec. 5.3.1.
- dnssec.works to fail02.dnssec.works: No valid RRSIGs made by a key corresponding to a DS RR were found covering the DNSKEY RRset, resulting in no secure entry point (SEP) into the zone. See RFC 4035, Sec. 2.2, RFC 6840, Sec. 5.11. (5.45.109.212, 185.92.221.212, 2001:19f0:5001:df:76d7:5703:ba0a:e220, 2a03:4000:6:2115::2, TCP_-_EDNS0_4096_D_K)
- fail02.dnssec.works zone: The server(s) were not responsive to queries over UDP. See RFC 1035, Sec. 4.2. (37.153.96.134)
- fail02.dnssec.works/A: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (37.153.96.134, UDP_-_NOEDNS_)
- fail02.dnssec.works/NS: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (37.153.96.134, UDP_-_NOEDNS_)
- fail02.dnssec.works/CNAME has errors; select the "Denial of existence" DNSSEC option to see them.
- fail02.dnssec.works/MX has errors; select the "Denial of existence" DNSSEC option to see them.
- fail02.dnssec.works/DNSKEY has errors; select the "Denial of existence" DNSSEC option to see them.
- t7dcrauv31.fail02.dnssec.works/A has errors; select the "Denial of existence" DNSSEC option to see them.
- fail02.dnssec.works/TXT has errors; select the "Denial of existence" DNSSEC option to see them.
Warnings (4)
- works/DS (alg 8, id 37126): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- works/DS (alg 8, id 37126): DNSSEC implementers are prohibited from implementing signing with DS algorithm 1 (SHA-1). See RFC 8624, Sec. 3.2.
- works/DS (alg 8, id 37126): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.
- works/DS (alg 8, id 37126): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset. See RFC 4509, Sec. 3.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.