disa.mil
Updated:
2024-08-20 14:42:42 UTC (143 days ago)
Go to most recent »
Notices
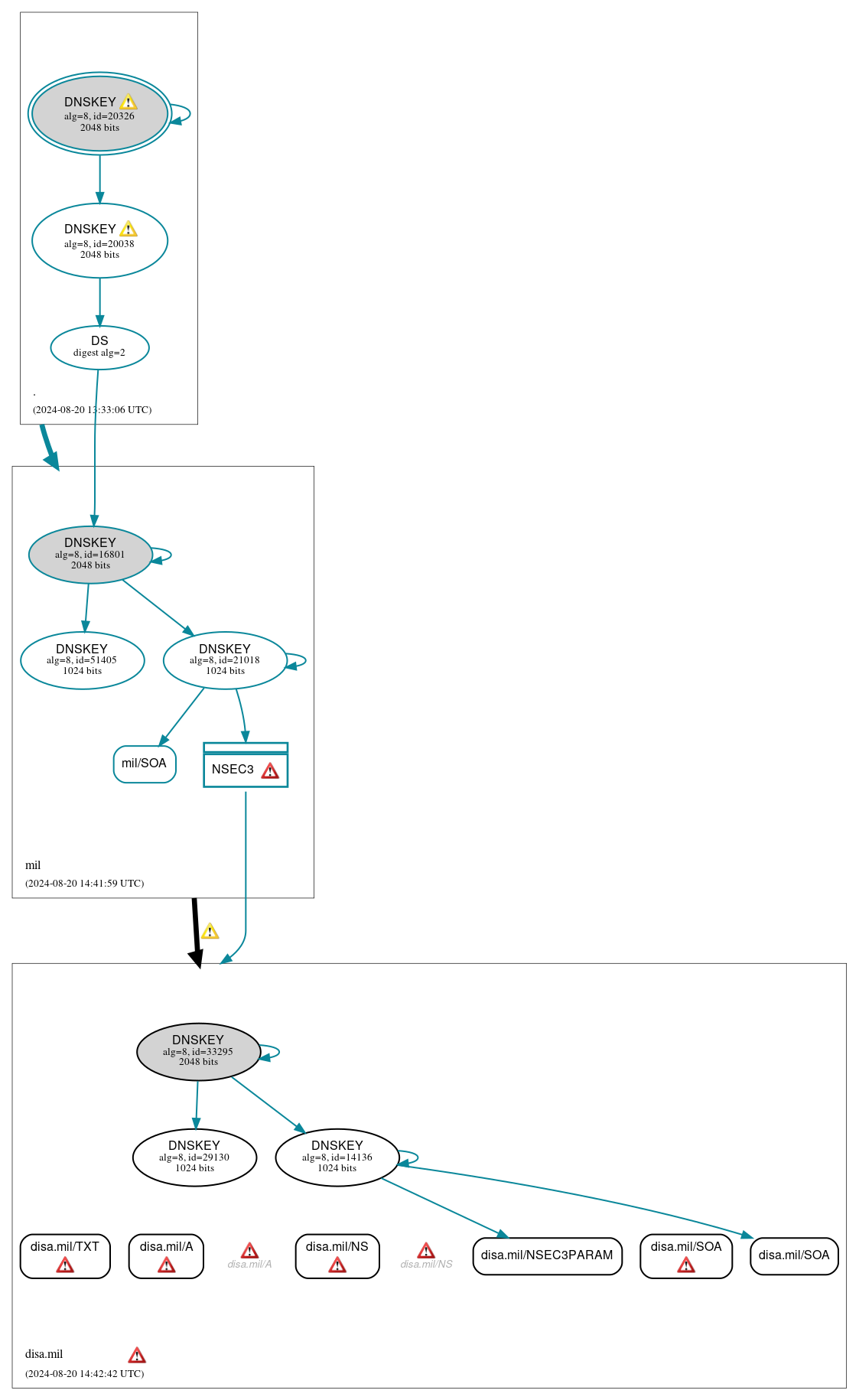
DNSSEC Authentication Chain
 RRset status
RRset status
Insecure (6)
- disa.mil/A
- disa.mil/NS
- disa.mil/NSEC3PARAM
- disa.mil/SOA
- disa.mil/SOA
- disa.mil/TXT
Secure (1)
- mil/SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Insecure (3)
- disa.mil/DNSKEY (alg 8, id 14136)
- disa.mil/DNSKEY (alg 8, id 29130)
- disa.mil/DNSKEY (alg 8, id 33295)
Secure (7)
- ./DNSKEY (alg 8, id 20038)
- ./DNSKEY (alg 8, id 20326)
- NSEC3 proving non-existence of disa.mil/DS
- mil/DNSKEY (alg 8, id 16801)
- mil/DNSKEY (alg 8, id 21018)
- mil/DNSKEY (alg 8, id 51405)
- mil/DS (alg 8, id 16801)
 Delegation status
Delegation status
Insecure (1)
- mil to disa.mil
Secure (1)
- . to mil
 Notices
Notices
Errors (16)
- NSEC3 proving non-existence of disa.mil/DS: An iterations count of 0 must be used in NSEC3 records to alleviate computational burdens. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of disa.mil/DS: An iterations count of 0 must be used in NSEC3 records to alleviate computational burdens. See RFC 9276, Sec. 3.1.
- disa.mil zone: The server(s) were not responsive to queries over UDP. See RFC 1035, Sec. 4.2. (2608:102:0:1811:1001:2000:c70:20, 2608:102:0:182d:1001:9012:c00:20, 2608:125:0:1811:1001:9012:f00:20, 2608:145:0:180b:1001:9012:d00:20, 2608:4122:0:1012:1001:9012:1400:20, 2608:c182::1001:9012:1600:20, 2608:c182:0:1012:1001:9012:1400:20)
- disa.mil/A: No RRSIG covering the RRset was returned in the response. See RFC 4035, Sec. 3.1.1. (131.77.60.232, 152.229.110.232, 214.3.125.232, 214.23.245.6, 215.65.126.185, UDP_-_EDNS0_4096_D_KN)
- disa.mil/A: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (2608:102:0:1811:1001:2000:c70:20, 2608:102:0:182d:1001:9012:c00:20, 2608:125:0:1811:1001:9012:f00:20, 2608:145:0:180b:1001:9012:d00:20, 2608:4122:0:1012:1001:9012:1400:20, 2608:c182::1001:9012:1600:20, 2608:c182:0:1012:1001:9012:1400:20, UDP_-_NOEDNS_)
- disa.mil/NS: No RRSIG covering the RRset was returned in the response. See RFC 4035, Sec. 3.1.1. (131.77.60.232, 152.229.110.232, 214.3.125.232, 214.23.245.6, 215.65.126.185, UDP_-_EDNS0_4096_D_KN)
- disa.mil/NS: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (2608:102:0:1811:1001:2000:c70:20, 2608:102:0:182d:1001:9012:c00:20, 2608:125:0:1811:1001:9012:f00:20, 2608:145:0:180b:1001:9012:d00:20, 2608:4122:0:1012:1001:9012:1400:20, 2608:c182::1001:9012:1600:20, 2608:c182:0:1012:1001:9012:1400:20, UDP_-_NOEDNS_)
- disa.mil/SOA: No RRSIG covering the RRset was returned in the response. See RFC 4035, Sec. 3.1.1. (152.229.110.232, 214.23.245.6, TCP_-_EDNS0_4096_D_N, UDP_-_EDNS0_4096_D_KN, UDP_-_EDNS0_4096_D_KN_0x20)
- disa.mil/TXT: No RRSIG covering the RRset was returned in the response. See RFC 4035, Sec. 3.1.1. (131.77.60.232, 152.229.110.232, 214.3.125.232, 214.23.245.6, 215.65.126.185, UDP_-_EDNS0_4096_D_KN)
- disa.mil/CDS has errors; select the "Denial of existence" DNSSEC option to see them.
- ip7cn.fp71j.disa.mil/A has errors; select the "Denial of existence" DNSSEC option to see them.
- disa.mil/MX has errors; select the "Denial of existence" DNSSEC option to see them.
- disa.mil/DS has errors; select the "Denial of existence" DNSSEC option to see them.
- disa.mil/CDNSKEY has errors; select the "Denial of existence" DNSSEC option to see them.
- disa.mil/CNAME has errors; select the "Denial of existence" DNSSEC option to see them.
- disa.mil/AAAA has errors; select the "Denial of existence" DNSSEC option to see them.
Warnings (13)
- ./DNSKEY (alg 8, id 20038): The server appears to support DNS cookies but did not return a COOKIE option. See RFC 7873, Sec. 5.2.3. (2001:500:2f::f, UDP_-_EDNS0_4096_D_KN)
- ./DNSKEY (alg 8, id 20326): The server appears to support DNS cookies but did not return a COOKIE option. See RFC 7873, Sec. 5.2.3. (2001:500:2f::f, UDP_-_EDNS0_4096_D_KN)
- NSEC3 proving non-existence of disa.mil/DS: The salt value for an NSEC3 record should be empty. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of disa.mil/DS: The salt value for an NSEC3 record should be empty. See RFC 9276, Sec. 3.1.
- mil to disa.mil: The glue address(es) for dns2.disa.mil (2608:102:0:1811:1001:2000:c70:20) differed from its authoritative address(es) (2608:102:0:182d:1001:9012:c00:20). See RFC 1034, Sec. 4.2.2.
- mil to disa.mil: The glue address(es) for dns4.disa.mil (2608:c182::1001:9012:1600:20) differed from its authoritative address(es) (2608:c182::1001:9012:1600:20, 2608:c182:0:1012:1001:9012:1400:20). See RFC 1034, Sec. 4.2.2.
- disa.mil/CDS has warnings; select the "Denial of existence" DNSSEC option to see them.
- disa.mil/AAAA has warnings; select the "Denial of existence" DNSSEC option to see them.
- disa.mil/MX has warnings; select the "Denial of existence" DNSSEC option to see them.
- disa.mil/DS has warnings; select the "Denial of existence" DNSSEC option to see them.
- disa.mil/CDNSKEY has warnings; select the "Denial of existence" DNSSEC option to see them.
- disa.mil/CNAME has warnings; select the "Denial of existence" DNSSEC option to see them.
- ip7cn.fp71j.disa.mil/A has warnings; select the "Denial of existence" DNSSEC option to see them.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.