commerce.gov
Updated:
2023-10-17 19:06:05 UTC (801 days ago)
Go to most recent »
Notices
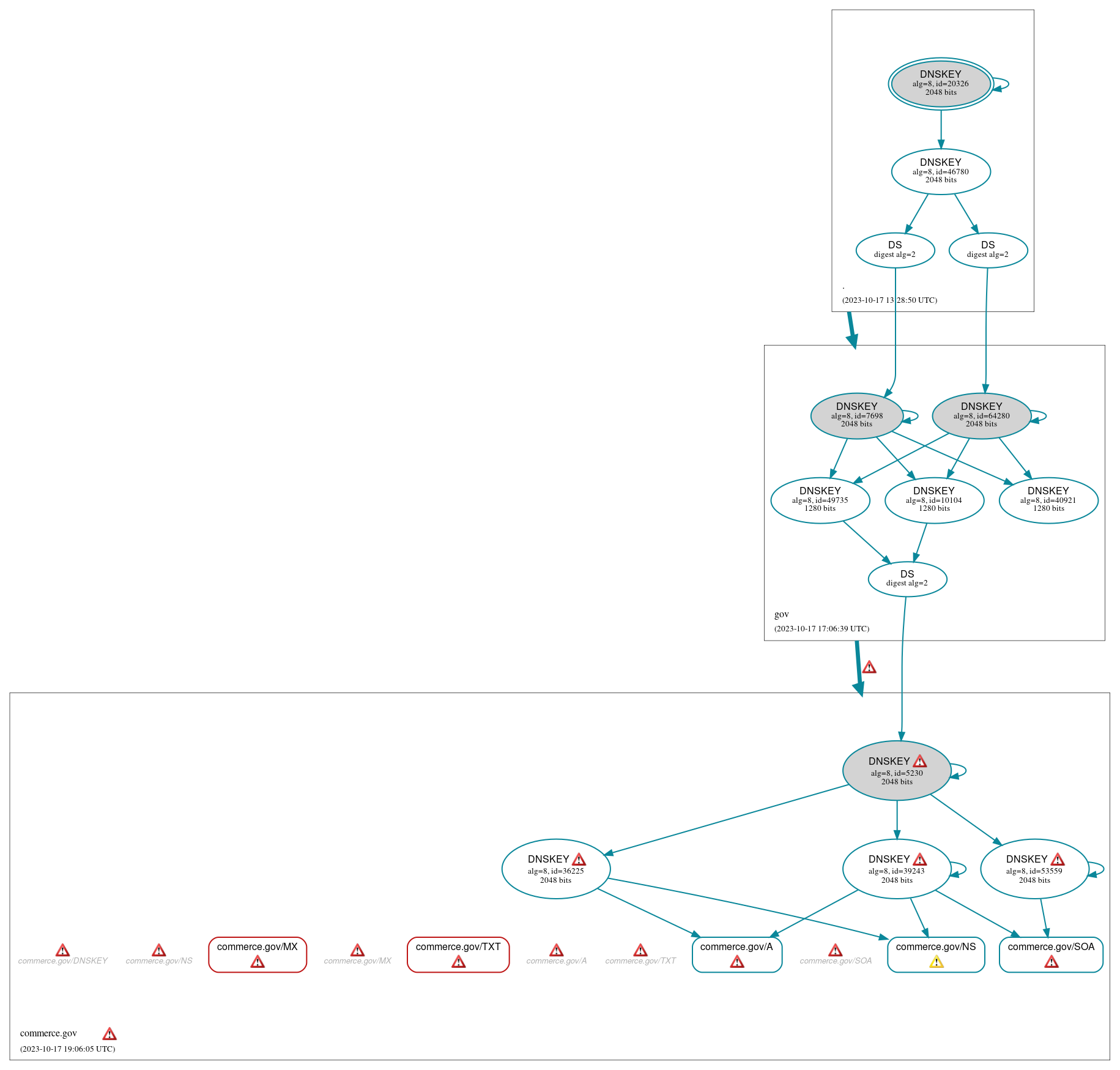
DNSSEC Authentication Chain
 RRset status
RRset status
Bogus (2)
- commerce.gov/MX
- commerce.gov/TXT
Secure (3)
- commerce.gov/A
- commerce.gov/NS
- commerce.gov/SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (14)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 46780)
- commerce.gov/DNSKEY (alg 8, id 36225)
- commerce.gov/DNSKEY (alg 8, id 39243)
- commerce.gov/DNSKEY (alg 8, id 5230)
- commerce.gov/DNSKEY (alg 8, id 53559)
- commerce.gov/DS (alg 8, id 5230)
- gov/DNSKEY (alg 8, id 10104)
- gov/DNSKEY (alg 8, id 40921)
- gov/DNSKEY (alg 8, id 49735)
- gov/DNSKEY (alg 8, id 64280)
- gov/DNSKEY (alg 8, id 7698)
- gov/DS (alg 8, id 64280)
- gov/DS (alg 8, id 7698)
 Delegation status
Delegation status
Secure (2)
- . to gov
- gov to commerce.gov
 Notices
Notices
Errors (54)
- RRSIG gov/DNSKEY alg 8, id 64280: The TTL of the RRset (86400) exceeds the value of the Original TTL field of the RRSIG RR covering it (3600). See RFC 4035, Sec. 2.2.
- RRSIG gov/DNSKEY alg 8, id 64280: The TTL of the RRset (86400) exceeds the value of the Original TTL field of the RRSIG RR covering it (3600). See RFC 4035, Sec. 2.2.
- RRSIG gov/DNSKEY alg 8, id 64280: The TTL of the RRset (86400) exceeds the value of the Original TTL field of the RRSIG RR covering it (3600). See RFC 4035, Sec. 2.2.
- RRSIG gov/DNSKEY alg 8, id 64280: The TTL of the RRset (86400) exceeds the value of the Original TTL field of the RRSIG RR covering it (3600). See RFC 4035, Sec. 2.2.
- RRSIG gov/DNSKEY alg 8, id 64280: The TTL of the RRset (86400) exceeds the value of the Original TTL field of the RRSIG RR covering it (3600). See RFC 4035, Sec. 2.2.
- commerce.gov zone: The server(s) responded over TCP with a malformed response or with an invalid RCODE. See RFC 1035, Sec. 4.1.1. (2001:470:1:7a::147)
- commerce.gov zone: The server(s) were not responsive to queries over TCP. See RFC 1035, Sec. 4.2. (170.110.225.13, 2610:20:0:20:d0c:90c:225:225)
- commerce.gov zone: The server(s) were not responsive to queries over UDP. See RFC 1035, Sec. 4.2. (170.110.225.11, 170.110.225.16, 192.198.87.242, 2001:49f0:d064:6:1000::237, 2001:49f0:d064:6:1000::238, 2607:5600:143:0:1000::101, 2610:20:0:20:d0c:90c:225:223)
- commerce.gov/A: DNSSEC was effectively downgraded because no response was received from the server over UDP (tried 10 times) with the DO bit set. See RFC 4035, Sec. 3.2.1. (198.255.114.190, UDP_-_EDNS0_4096_)
- commerce.gov/A: DNSSEC was effectively downgraded because no response was received from the server over UDP (tried 11 times) with EDNS enabled. See RFC 6891, Sec. 7, RFC 2671, Sec. 5.3. (64.62.200.147, UDP_-_NOEDNS_)
- commerce.gov/A: No response was received from the server over UDP (tried 10 times) until the DO EDNS flag was cleared (however, this server appeared to respond legitimately to other queries with the DO EDNS flag set). See RFC 6891, Sec. 6.1.4. (198.255.114.190, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/A: No response was received from the server over UDP (tried 11 times) until EDNS was disabled (however, this server appeared to respond legitimately to other queries with EDNS enabled). See RFC 6891, Sec. 6.2.6. (64.62.200.147, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/A: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (170.110.225.11, 170.110.225.16, 192.198.87.242, 2001:49f0:d064:6:1000::237, 2001:49f0:d064:6:1000::238, 2607:5600:143:0:1000::101, 2610:20:0:20:d0c:90c:225:223, UDP_-_NOEDNS_)
- commerce.gov/A: The DNSSEC records necessary to validate the response could not be retrieved from the server. See RFC 4035, Sec. 3.1.1, RFC 4035, Sec. 3.1.3. (64.62.200.147, 198.255.114.190, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/DNSKEY (alg 8, id 36225): DNSSEC was effectively downgraded because no response was received from the server over UDP (tried 11 times) with EDNS enabled. See RFC 6891, Sec. 7, RFC 2671, Sec. 5.3. (64.62.200.147, TCP_-_NOEDNS_)
- commerce.gov/DNSKEY (alg 8, id 36225): No response was received from the server over UDP (tried 11 times) until EDNS was disabled (however, this server appeared to respond legitimately to other queries with EDNS enabled). See RFC 6891, Sec. 6.2.6. (64.62.200.147, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/DNSKEY (alg 8, id 36225): The DNSSEC records necessary to validate the response could not be retrieved from the server. See RFC 4035, Sec. 3.1.1, RFC 4035, Sec. 3.1.3. (64.62.200.147, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/DNSKEY (alg 8, id 39243): DNSSEC was effectively downgraded because no response was received from the server over UDP (tried 11 times) with EDNS enabled. See RFC 6891, Sec. 7, RFC 2671, Sec. 5.3. (64.62.200.147, TCP_-_NOEDNS_)
- commerce.gov/DNSKEY (alg 8, id 39243): No response was received from the server over UDP (tried 11 times) until EDNS was disabled (however, this server appeared to respond legitimately to other queries with EDNS enabled). See RFC 6891, Sec. 6.2.6. (64.62.200.147, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/DNSKEY (alg 8, id 39243): The DNSSEC records necessary to validate the response could not be retrieved from the server. See RFC 4035, Sec. 3.1.1, RFC 4035, Sec. 3.1.3. (64.62.200.147, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/DNSKEY (alg 8, id 5230): DNSSEC was effectively downgraded because no response was received from the server over UDP (tried 11 times) with EDNS enabled. See RFC 6891, Sec. 7, RFC 2671, Sec. 5.3. (64.62.200.147, TCP_-_NOEDNS_)
- commerce.gov/DNSKEY (alg 8, id 5230): No response was received from the server over UDP (tried 11 times) until EDNS was disabled (however, this server appeared to respond legitimately to other queries with EDNS enabled). See RFC 6891, Sec. 6.2.6. (64.62.200.147, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/DNSKEY (alg 8, id 5230): The DNSSEC records necessary to validate the response could not be retrieved from the server. See RFC 4035, Sec. 3.1.1, RFC 4035, Sec. 3.1.3. (64.62.200.147, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/DNSKEY (alg 8, id 53559): DNSSEC was effectively downgraded because no response was received from the server over UDP (tried 11 times) with EDNS enabled. See RFC 6891, Sec. 7, RFC 2671, Sec. 5.3. (64.62.200.147, TCP_-_NOEDNS_)
- commerce.gov/DNSKEY (alg 8, id 53559): No response was received from the server over UDP (tried 11 times) until EDNS was disabled (however, this server appeared to respond legitimately to other queries with EDNS enabled). See RFC 6891, Sec. 6.2.6. (64.62.200.147, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/DNSKEY (alg 8, id 53559): The DNSSEC records necessary to validate the response could not be retrieved from the server. See RFC 4035, Sec. 3.1.1, RFC 4035, Sec. 3.1.3. (64.62.200.147, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/DNSKEY: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (170.110.225.13, 198.255.114.189, 198.255.114.190, 2610:20:0:20:d0c:90c:225:225, UDP_-_NOEDNS_)
- commerce.gov/DNSKEY: No response was received from the server over UDP (tried 4 times). See RFC 1035, Sec. 4.2. (64.62.200.147, 170.110.225.13, 198.255.114.189, 198.255.114.190, 2610:20:0:20:d0c:90c:225:225, UDP_-_EDNS0_512_D_KN)
- commerce.gov/MX: DNSSEC was effectively downgraded because no response was received from the server over UDP (tried 11 times) with EDNS enabled. See RFC 6891, Sec. 7, RFC 2671, Sec. 5.3. (64.62.200.147, UDP_-_NOEDNS_)
- commerce.gov/MX: No response was received from the server over TCP (tried 6 times). See RFC 1035, Sec. 4.2. (198.255.114.189, TCP_-_EDNS0_4096_)
- commerce.gov/MX: No response was received from the server over TCP (tried 8 times). See RFC 1035, Sec. 4.2. (198.255.114.190, TCP_-_EDNS0_4096_D)
- commerce.gov/MX: No response was received from the server over UDP (tried 11 times) until EDNS was disabled (however, this server appeared to respond legitimately to other queries with EDNS enabled). See RFC 6891, Sec. 6.2.6. (64.62.200.147, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/MX: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (170.110.225.13, 2001:470:1:7a::147, 2610:20:0:20:d0c:90c:225:225, UDP_-_EDNS0_4096_D_KN, UDP_-_NOEDNS_)
- commerce.gov/MX: No response was received from the server over UDP (tried 4 times). See RFC 1035, Sec. 4.2. (64.62.200.147, 170.110.225.13, 198.255.114.189, 198.255.114.190, 2610:20:0:20:d0c:90c:225:225, UDP_-_EDNS0_512_D_KN)
- commerce.gov/MX: The DNSSEC records necessary to validate the response could not be retrieved from the server. See RFC 4035, Sec. 3.1.1, RFC 4035, Sec. 3.1.3. (64.62.200.147, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/NS: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (170.110.225.11, 170.110.225.13, 170.110.225.16, 192.198.87.242, 198.255.114.190, 2001:470:1:7a::147, 2001:49f0:d064:6:1000::237, 2001:49f0:d064:6:1000::238, 2607:5600:143:0:1000::101, 2610:20:0:20:d0c:90c:225:223, 2610:20:0:20:d0c:90c:225:225, UDP_-_NOEDNS_)
- commerce.gov/SOA: DNSSEC was effectively downgraded because no response was received from the server over UDP (tried 10 times) with the DO bit set. See RFC 4035, Sec. 3.2.1. (198.255.114.190, UDP_-_EDNS0_4096_)
- commerce.gov/SOA: No response was received from the server over TCP (tried 3 times). See RFC 1035, Sec. 4.2. (198.255.114.189, 2001:470:1:7a::147, TCP_-_EDNS0_4096_D, TCP_-_EDNS0_4096_D_N)
- commerce.gov/SOA: No response was received from the server over TCP (tried 4 times). See RFC 1035, Sec. 4.2. (170.110.225.13, 2610:20:0:20:d0c:90c:225:225, TCP_-_EDNS0_4096_D_N)
- commerce.gov/SOA: No response was received from the server over TCP (tried 5 times). See RFC 1035, Sec. 4.2. (2001:470:1:7a::147, TCP_-_EDNS0_4096_D_KN_0x20)
- commerce.gov/SOA: No response was received from the server over UDP (tried 10 times) until the DO EDNS flag was cleared (however, this server appeared to respond legitimately to other queries with the DO EDNS flag set). See RFC 6891, Sec. 6.1.4. (198.255.114.190, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/SOA: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (170.110.225.13, 198.255.114.189, 198.255.114.190, 2610:20:0:20:d0c:90c:225:225, UDP_-_NOEDNS_, UDP_-_NOEDNS__0x20)
- commerce.gov/SOA: The DNSSEC records necessary to validate the response could not be retrieved from the server. See RFC 4035, Sec. 3.1.1, RFC 4035, Sec. 3.1.3. (198.255.114.190, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/TXT: DNSSEC was effectively downgraded because no response was received from the server over UDP (tried 10 times) with the DO bit set. See RFC 4035, Sec. 3.2.1. (198.255.114.190, UDP_-_EDNS0_4096_)
- commerce.gov/TXT: No response was received from the server over UDP (tried 10 times) until the DO EDNS flag was cleared (however, this server appeared to respond legitimately to other queries with the DO EDNS flag set). See RFC 6891, Sec. 6.1.4. (198.255.114.190, UDP_-_EDNS0_4096_D_KN)
- commerce.gov/TXT: No response was received from the server over UDP (tried 12 times). See RFC 1035, Sec. 4.2. (64.62.200.147, 170.110.225.13, 198.255.114.189, 2001:470:1:7a::147, 2610:20:0:20:d0c:90c:225:225, UDP_-_NOEDNS_)
- commerce.gov/TXT: The DNSSEC records necessary to validate the response could not be retrieved from the server. See RFC 4035, Sec. 3.1.1, RFC 4035, Sec. 3.1.3. (198.255.114.190, UDP_-_EDNS0_4096_D_KN)
- gov to commerce.gov: No valid RRSIGs made by a key corresponding to a DS RR were found covering the DNSKEY RRset, resulting in no secure entry point (SEP) into the zone. See RFC 4035, Sec. 2.2, RFC 6840, Sec. 5.11. (64.62.200.147, TCP_-_NOEDNS_)
- gov to commerce.gov: The DS RRset for the zone included algorithm 8 (RSASHA256), but no DS RR matched a DNSKEY with algorithm 8 that signs the zone's DNSKEY RRset. See RFC 4035, Sec. 2.2, RFC 6840, Sec. 5.11. (64.62.200.147, TCP_-_NOEDNS_)
- commerce.gov/AAAA has errors; select the "Denial of existence" DNSSEC option to see them.
- commerce.gov/NSEC3PARAM has errors; select the "Denial of existence" DNSSEC option to see them.
- commerce.gov/CNAME has errors; select the "Denial of existence" DNSSEC option to see them.
- commerce.gov/DNSKEY has errors; select the "Denial of existence" DNSSEC option to see them.
- 2649xk3jat.commerce.gov/A has errors; select the "Denial of existence" DNSSEC option to see them.
Warnings (6)
- commerce.gov/NS: No response was received from the server over UDP (tried 6 times) until the COOKIE EDNS option was removed (however, this server appeared to respond legitimately to other queries with the COOKIE EDNS option present). See RFC 6891, Sec. 6.1.2. (198.255.114.189, UDP_-_EDNS0_4096_D_KN)
- gov to commerce.gov: Authoritative AAAA records exist for gpaens2.doc.gov, but there are no corresponding AAAA glue records. See RFC 1034, Sec. 4.2.2.
- gov to commerce.gov: Authoritative AAAA records exist for hchbens1.doc.gov, but there are no corresponding AAAA glue records. See RFC 1034, Sec. 4.2.2.
- gov to commerce.gov: The following NS name(s) were found in the delegation NS RRset (i.e., in the gov zone), but not in the authoritative NS RRset: hchbens2.doc.gov See RFC 1034, Sec. 4.2.2.
- commerce.gov/AAAA has warnings; select the "Denial of existence" DNSSEC option to see them.
- commerce.gov/NSEC3PARAM has warnings; select the "Denial of existence" DNSSEC option to see them.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.