ad5ey.net
Updated:
2024-07-24 19:25:00 UTC (123 days ago)
Go to most recent »
Notices
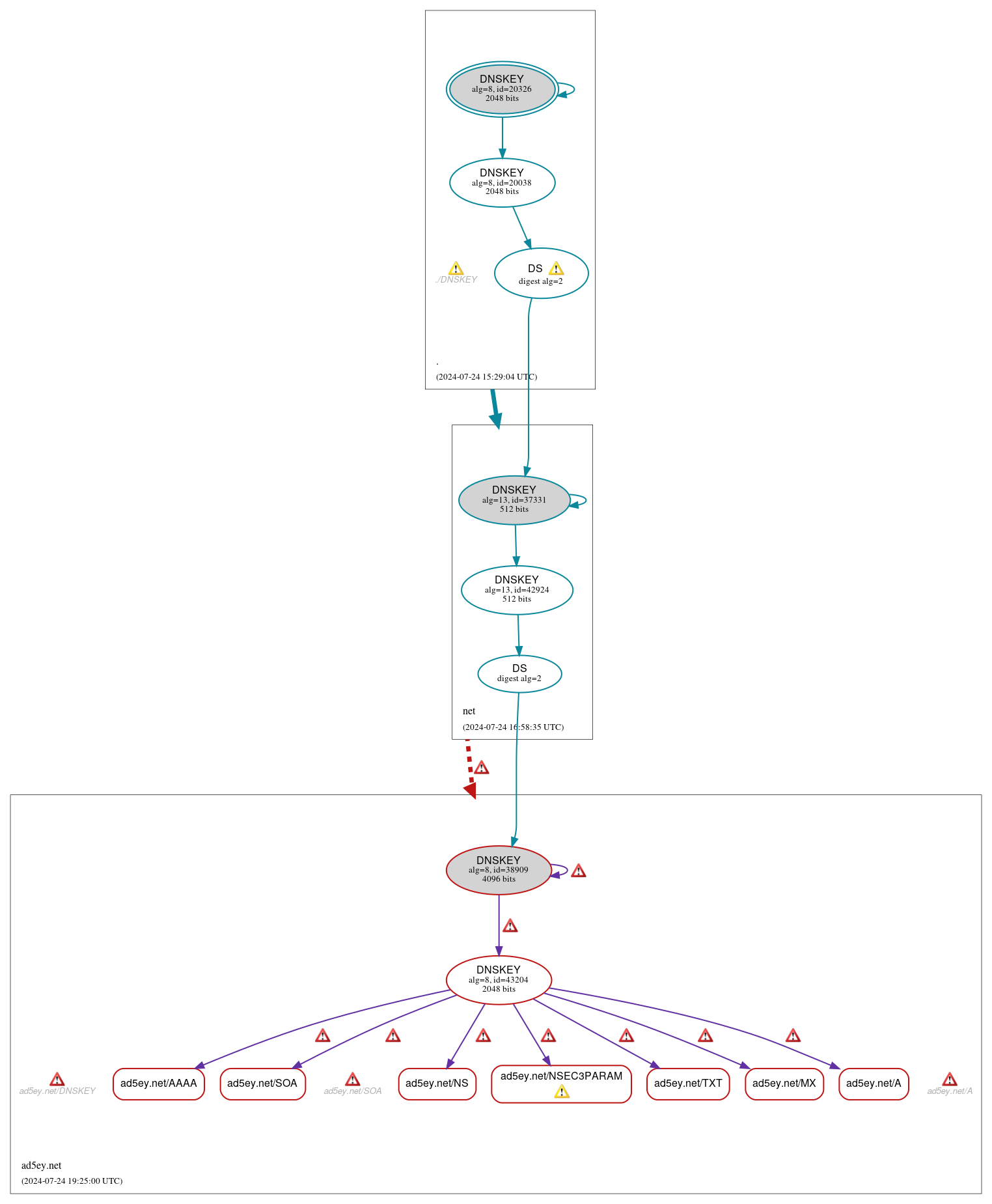
DNSSEC Authentication Chain
 RRset status
RRset status
Bogus (7)
- ad5ey.net/A
- ad5ey.net/AAAA
- ad5ey.net/MX
- ad5ey.net/NS
- ad5ey.net/NSEC3PARAM
- ad5ey.net/SOA
- ad5ey.net/TXT
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Bogus (2)
- ad5ey.net/DNSKEY (alg 8, id 38909)
- ad5ey.net/DNSKEY (alg 8, id 43204)
Secure (6)
- ./DNSKEY (alg 8, id 20038)
- ./DNSKEY (alg 8, id 20326)
- ad5ey.net/DS (alg 8, id 38909)
- net/DNSKEY (alg 13, id 37331)
- net/DNSKEY (alg 13, id 42924)
- net/DS (alg 13, id 37331)
 Delegation status
Delegation status
Bogus (1)
- net to ad5ey.net
Secure (1)
- . to net
 Notices
Notices
Errors (19)
- RRSIG ad5ey.net/A alg 8, id 43204: The Signature Expiration field of the RRSIG RR (2024-07-23 16:09:08+00:00) is 1 day in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG ad5ey.net/AAAA alg 8, id 43204: The Signature Expiration field of the RRSIG RR (2024-07-23 16:09:08+00:00) is 1 day in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG ad5ey.net/DNSKEY alg 8, id 38909: The Signature Expiration field of the RRSIG RR (2024-07-23 16:09:08+00:00) is 1 day in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG ad5ey.net/DNSKEY alg 8, id 38909: The Signature Expiration field of the RRSIG RR (2024-07-23 16:09:08+00:00) is 1 day in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG ad5ey.net/MX alg 8, id 43204: The Signature Expiration field of the RRSIG RR (2024-07-23 16:09:08+00:00) is 1 day in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG ad5ey.net/NS alg 8, id 43204: The Signature Expiration field of the RRSIG RR (2024-07-23 16:09:08+00:00) is 1 day in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG ad5ey.net/NSEC3PARAM alg 8, id 43204: The Signature Expiration field of the RRSIG RR (2024-07-23 16:09:08+00:00) is 1 day in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG ad5ey.net/SOA alg 8, id 43204: The Signature Expiration field of the RRSIG RR (2024-07-23 16:09:08+00:00) is 1 day in the past. See RFC 4035, Sec. 5.3.1.
- RRSIG ad5ey.net/TXT alg 8, id 43204: The Signature Expiration field of the RRSIG RR (2024-07-23 16:09:08+00:00) is 1 day in the past. See RFC 4035, Sec. 5.3.1.
- ad5ey.net/A: The UDP connection was refused (ECONNREFUSED). See RFC 1035, Sec. 4.2. (216.66.80.18, UDP_-_EDNS0_4096_D_KN)
- ad5ey.net/DNSKEY: The UDP connection was refused (ECONNREFUSED). See RFC 1035, Sec. 4.2. (216.66.80.18, UDP_-_EDNS0_4096_D_N)
- ad5ey.net/SOA: No response was received from the server over UDP (tried 14 times). See RFC 1035, Sec. 4.2. (216.66.80.18, UDP_-_EDNS0_4096_D_KN_0x20)
- ad5ey.net/SOA: The UDP connection was refused (ECONNREFUSED). See RFC 1035, Sec. 4.2. (216.66.80.18, UDP_-_EDNS0_4096_D_KN)
- net to ad5ey.net: No valid RRSIGs made by a key corresponding to a DS RR were found covering the DNSKEY RRset, resulting in no secure entry point (SEP) into the zone. See RFC 4035, Sec. 2.2, RFC 6840, Sec. 5.11. (96.126.100.165, 173.255.213.159, 216.66.1.2, 216.218.130.2, 216.218.131.2, 216.218.132.2, 2001:470:100::2, 2001:470:200::2, 2001:470:300::2, 2001:470:400::2, 2001:470:500::2, 2600:3c01::f03c:91ff:fedf:87cd, 2600:3c01::f03c:93ff:fe99:222f, TCP_-_EDNS0_4096_D_KN)
- ad5ey.net/CDNSKEY has errors; select the "Denial of existence" DNSSEC option to see them.
- r9pmf.2kya9.ad5ey.net/A has errors; select the "Denial of existence" DNSSEC option to see them.
- ad5ey.net/CNAME has errors; select the "Denial of existence" DNSSEC option to see them.
- ad5ey.net/DNSKEY has errors; select the "Denial of existence" DNSSEC option to see them.
- ad5ey.net/CDS has errors; select the "Denial of existence" DNSSEC option to see them.
Warnings (8)
- ./DNSKEY: The server appears to support DNS cookies but did not return a COOKIE option. See RFC 7873, Sec. 5.2.3. (2001:500:2f::f, UDP_-_EDNS0_512_D_KN)
- ad5ey.net/NSEC3PARAM: No response was received until the UDP payload size was decreased, indicating that the server might be attempting to send a payload that exceeds the path maximum transmission unit (PMTU) size. See RFC 6891, Sec. 6.2.6. (216.66.80.18, UDP_-_EDNS0_4096_D_KN)
- net/DS (alg 13, id 37331): The server appears to support DNS cookies but did not return a COOKIE option. See RFC 7873, Sec. 5.2.3. (2001:500:2f::f, UDP_-_EDNS0_4096_D_KN)
- net/DS (alg 13, id 37331): The server appears to support DNS cookies but did not return a COOKIE option. See RFC 7873, Sec. 5.2.3. (2001:500:2f::f, UDP_-_EDNS0_4096_D_KN)
- ad5ey.net/CDNSKEY has warnings; select the "Denial of existence" DNSSEC option to see them.
- ad5ey.net/CDS has warnings; select the "Denial of existence" DNSSEC option to see them.
- ad5ey.net/CNAME has warnings; select the "Denial of existence" DNSSEC option to see them.
- r9pmf.2kya9.ad5ey.net/A has warnings; select the "Denial of existence" DNSSEC option to see them.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.