wm.com
Updated:
2022-01-26 16:38:04 UTC (819 days ago)
Update now
Notices
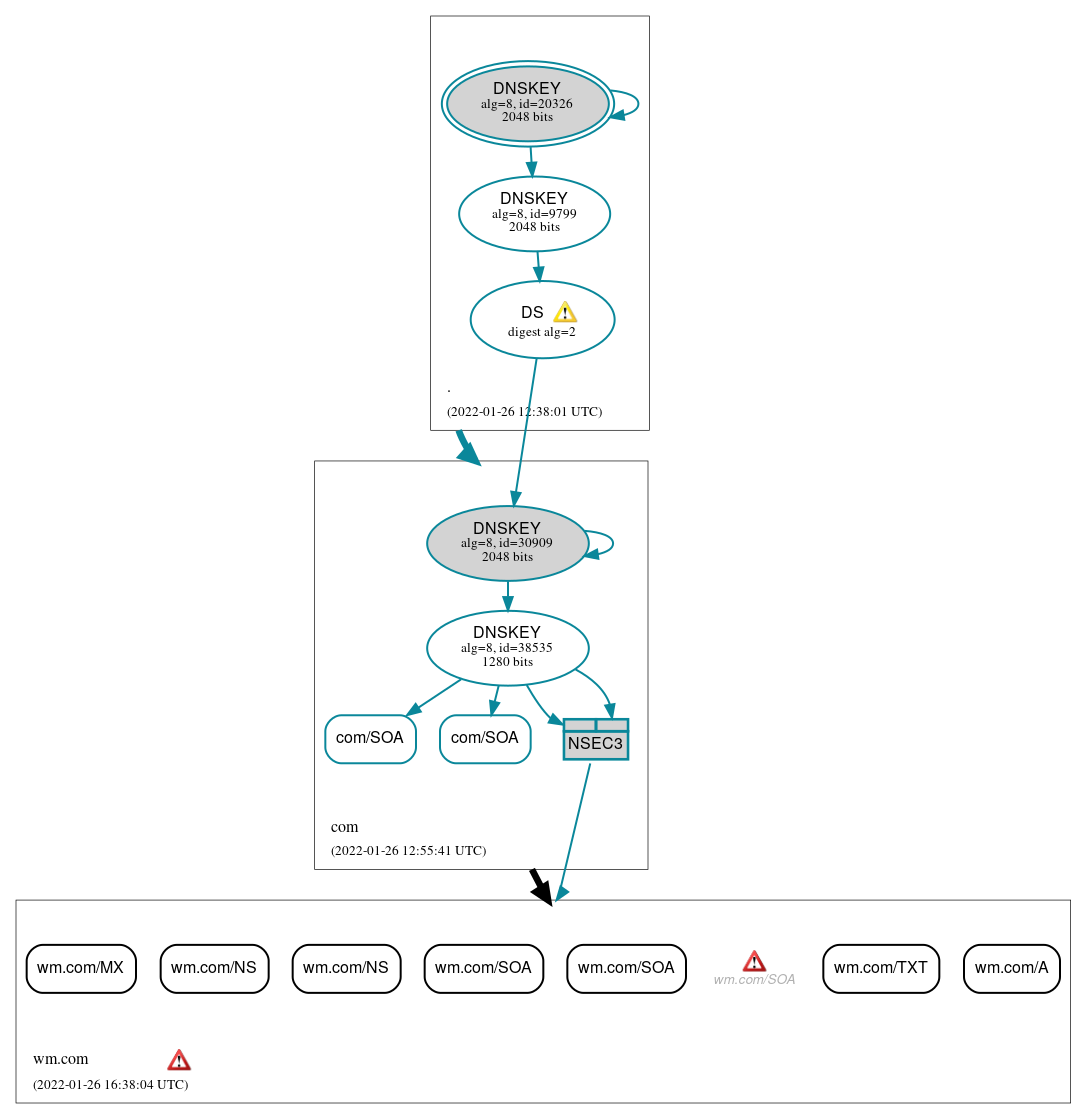
DNSSEC Authentication Chain
 RRset status
RRset status
Insecure (7)
- wm.com/A
- wm.com/MX
- wm.com/NS
- wm.com/NS
- wm.com/SOA
- wm.com/SOA
- wm.com/TXT
Secure (2)
- com/SOA
- com/SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (6)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 9799)
- NSEC3 proving non-existence of wm.com/DS
- com/DNSKEY (alg 8, id 30909)
- com/DNSKEY (alg 8, id 38535)
- com/DS (alg 8, id 30909)
 Delegation status
Delegation status
Insecure (1)
- com to wm.com
Secure (1)
- . to com
 Notices
Notices
Errors (2)
- wm.com zone: The server(s) were not responsive to queries over TCP. (156.101.1.48, 156.101.1.49)
- wm.com/SOA: No response was received from the server over TCP (tried 3 times). (156.101.1.48, 156.101.1.49, TCP_-_EDNS0_4096_D_N)
Warnings (2)
- com/DS (alg 8, id 30909): No response was received until the UDP payload size was decreased, indicating that the server might be attempting to send a payload that exceeds the path maximum transmission unit (PMTU) size. (192.203.230.10, UDP_-_EDNS0_4096_D_KN)
- com/DS (alg 8, id 30909): No response was received until the UDP payload size was decreased, indicating that the server might be attempting to send a payload that exceeds the path maximum transmission unit (PMTU) size. (192.203.230.10, UDP_-_EDNS0_4096_D_KN)





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.