wagner.edu
Updated:
2021-03-31 17:16:19 UTC (1385 days ago)
Update now
Notices
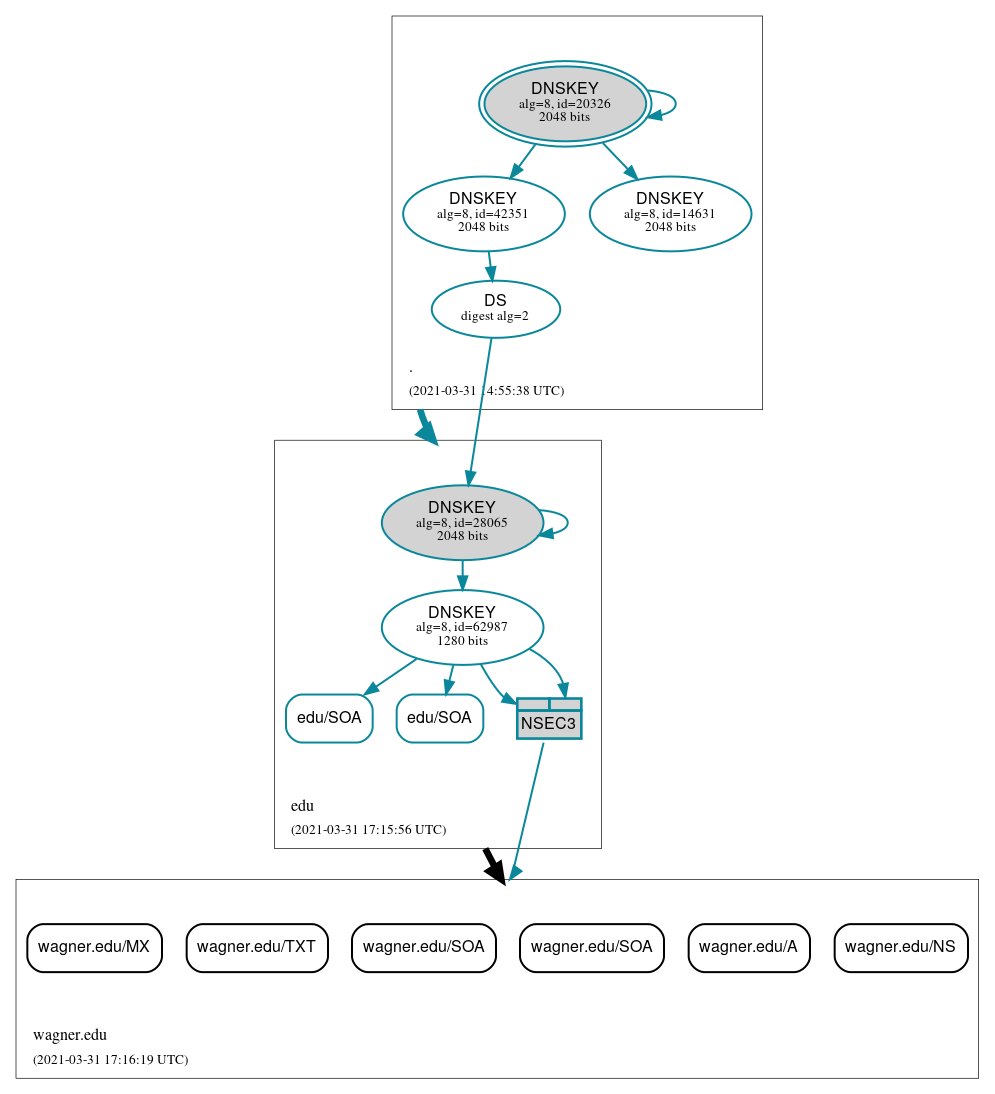
DNSSEC Authentication Chain
 RRset status
RRset status
Insecure (6)
- wagner.edu/A
- wagner.edu/MX
- wagner.edu/NS
- wagner.edu/SOA
- wagner.edu/SOA
- wagner.edu/TXT
Secure (2)
- edu/SOA
- edu/SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (7)
- ./DNSKEY (alg 8, id 14631)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 42351)
- NSEC3 proving non-existence of wagner.edu/DS
- edu/DNSKEY (alg 8, id 28065)
- edu/DNSKEY (alg 8, id 62987)
- edu/DS (alg 8, id 28065)
 Delegation status
Delegation status
Insecure (1)
- edu to wagner.edu
Secure (1)
- . to edu





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.