vecs.cs.ovgu.de
Updated:
2020-11-11 03:38:24 UTC (1519 days ago)
Update now
Notices
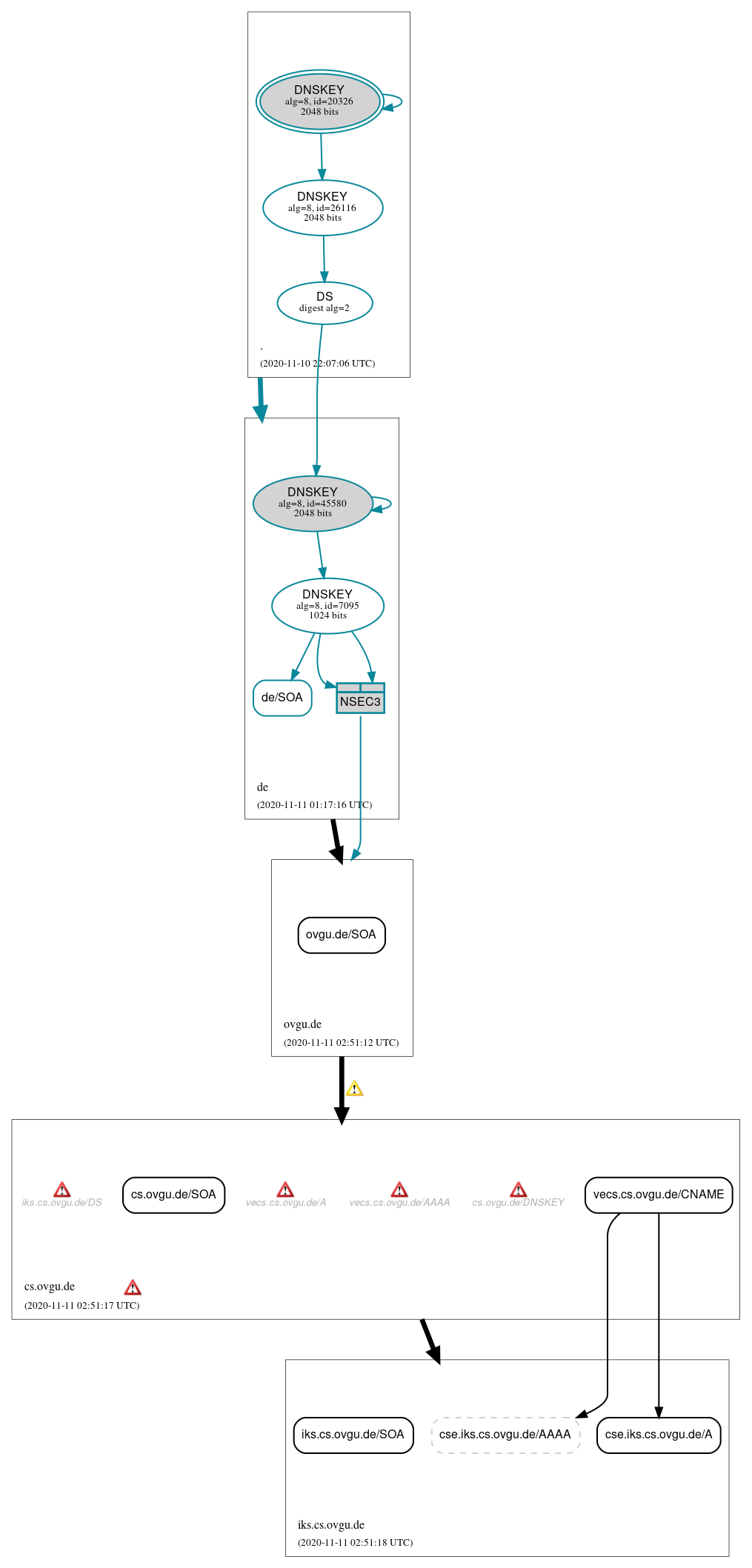
DNSSEC Authentication Chain
 RRset status
RRset status
Insecure (6)
- cs.ovgu.de/SOA
- cse.iks.cs.ovgu.de/A
- cse.iks.cs.ovgu.de/AAAA (NODATA)
- iks.cs.ovgu.de/SOA
- ovgu.de/SOA
- vecs.cs.ovgu.de/CNAME
Secure (1)
- de/SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (6)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 26116)
- NSEC3 proving non-existence of ovgu.de/DS
- de/DNSKEY (alg 8, id 45580)
- de/DNSKEY (alg 8, id 7095)
- de/DS (alg 8, id 45580)
 Delegation status
Delegation status
Insecure (3)
- cs.ovgu.de to iks.cs.ovgu.de
- de to ovgu.de
- ovgu.de to cs.ovgu.de
Secure (1)
- . to de
 Notices
Notices
Errors (8)
- NSEC3 proving non-existence of ovgu.de/DS: An iterations count of 0 must be used in NSEC3 records to alleviate computational burdens. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of ovgu.de/DS: An iterations count of 0 must be used in NSEC3 records to alleviate computational burdens. See RFC 9276, Sec. 3.1.
- cs.ovgu.de zone: The server(s) responded over UDP with a malformed response or with an invalid RCODE. See RFC 1035, Sec. 4.1.1. (141.44.23.1)
- cs.ovgu.de/DNSKEY: The response had an invalid RCODE (REFUSED). See RFC 1035, Sec. 4.1.1. (141.44.23.1, UDP_-_EDNS0_4096_D_K, UDP_-_EDNS0_512_D_K)
- iks.cs.ovgu.de/DS: The response had an invalid RCODE (REFUSED). See RFC 1035, Sec. 4.1.1. (141.44.23.1, UDP_-_EDNS0_4096_D_K)
- vecs.cs.ovgu.de/A: The response had an invalid RCODE (REFUSED). See RFC 1035, Sec. 4.1.1. (141.44.23.1, UDP_-_EDNS0_4096_D_K)
- vecs.cs.ovgu.de/AAAA: The response had an invalid RCODE (REFUSED). See RFC 1035, Sec. 4.1.1. (141.44.23.1, UDP_-_EDNS0_4096_D_K)
- cs.ovgu.de/CNAME has errors; select the "Denial of existence" DNSSEC option to see them.
Warnings (4)
- NSEC3 proving non-existence of ovgu.de/DS: The salt value for an NSEC3 record should be empty. See RFC 9276, Sec. 3.1.
- NSEC3 proving non-existence of ovgu.de/DS: The salt value for an NSEC3 record should be empty. See RFC 9276, Sec. 3.1.
- ovgu.de to cs.ovgu.de: The following NS name(s) were found in the authoritative NS RRset, but not in the delegation NS RRset (i.e., in the ovgu.de zone): luxator.cs.ovgu.de, ns2.cs.ovgu.de, ns.cs.ovgu.de See RFC 1034, Sec. 4.2.2.
- ovgu.de to cs.ovgu.de: The following NS name(s) were found in the delegation NS RRset (i.e., in the ovgu.de zone), but not in the authoritative NS RRset: ns.cs.uni-magdeburg.de, ns2.cs.uni-magdeburg.de See RFC 1034, Sec. 4.2.2.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.