spikar.gr
Updated:
2025-12-03 18:05:30 UTC (5 days ago)
Update now
Notices
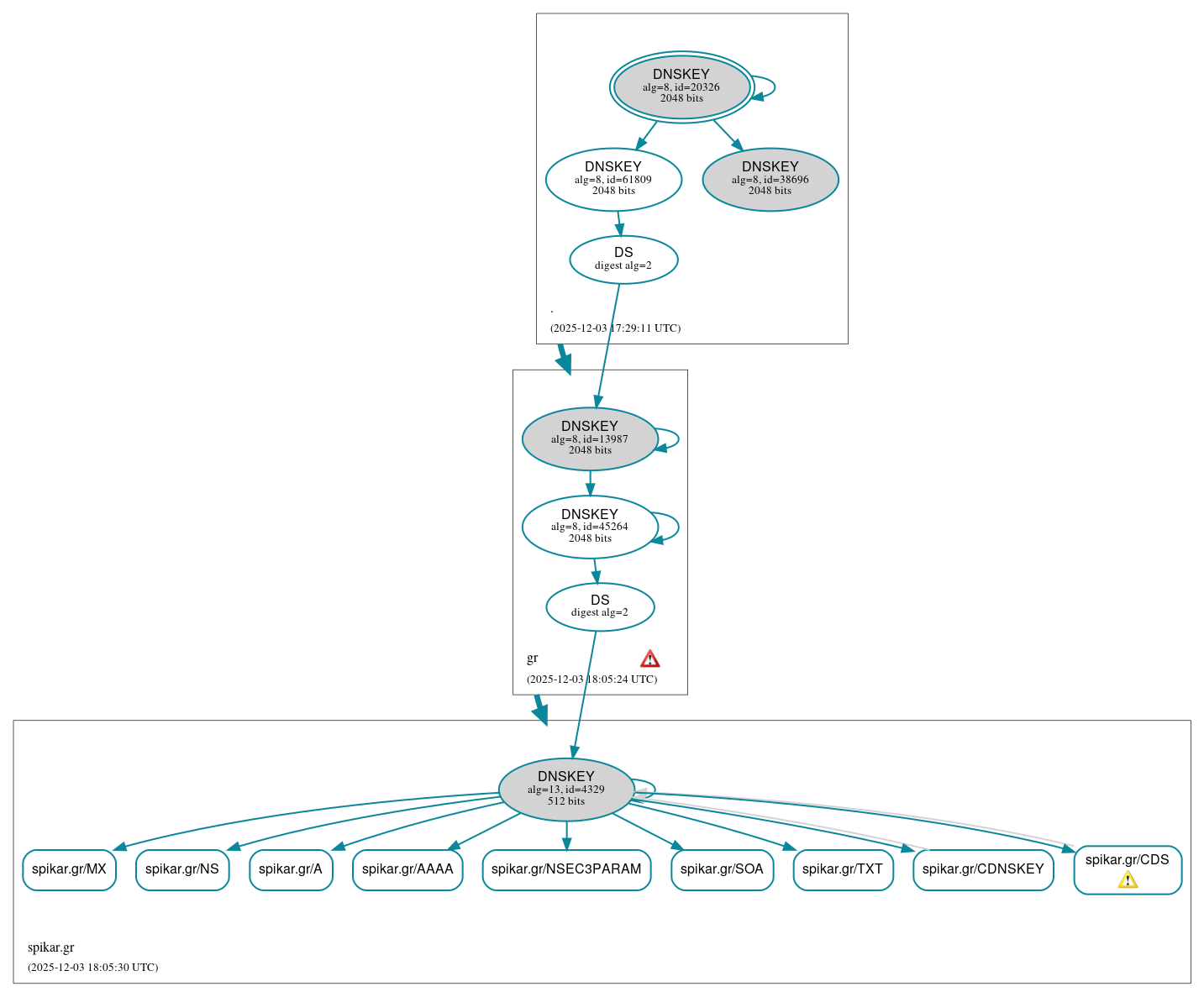
DNSSEC Authentication Chain
 RRset status
RRset status
Secure (9)
- spikar.gr/A
- spikar.gr/AAAA
- spikar.gr/CDNSKEY
- spikar.gr/CDS
- spikar.gr/MX
- spikar.gr/NS
- spikar.gr/NSEC3PARAM
- spikar.gr/SOA
- spikar.gr/TXT
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (8)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 38696)
- ./DNSKEY (alg 8, id 61809)
- gr/DNSKEY (alg 8, id 13987)
- gr/DNSKEY (alg 8, id 45264)
- gr/DS (alg 8, id 13987)
- spikar.gr/DNSKEY (alg 13, id 4329)
- spikar.gr/DS (alg 13, id 4329)
 Delegation status
Delegation status
Secure (2)
- . to gr
- gr to spikar.gr
 Notices
Notices
Errors (1)
- gr zone: The server(s) were not responsive to queries over UDP. See RFC 1035, Sec. 4.2. (2001:678:7::4:10)
Warnings (1)
- spikar.gr/CDS: The contents of the DS RRset are inconsistent with those of the CDS RRset. See RFC 7344, Sec. 3, RFC 7344, Sec. 5.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.