normandystyle.site
Updated:
2022-06-04 19:57:32 UTC (703 days ago)
Update now
Notices
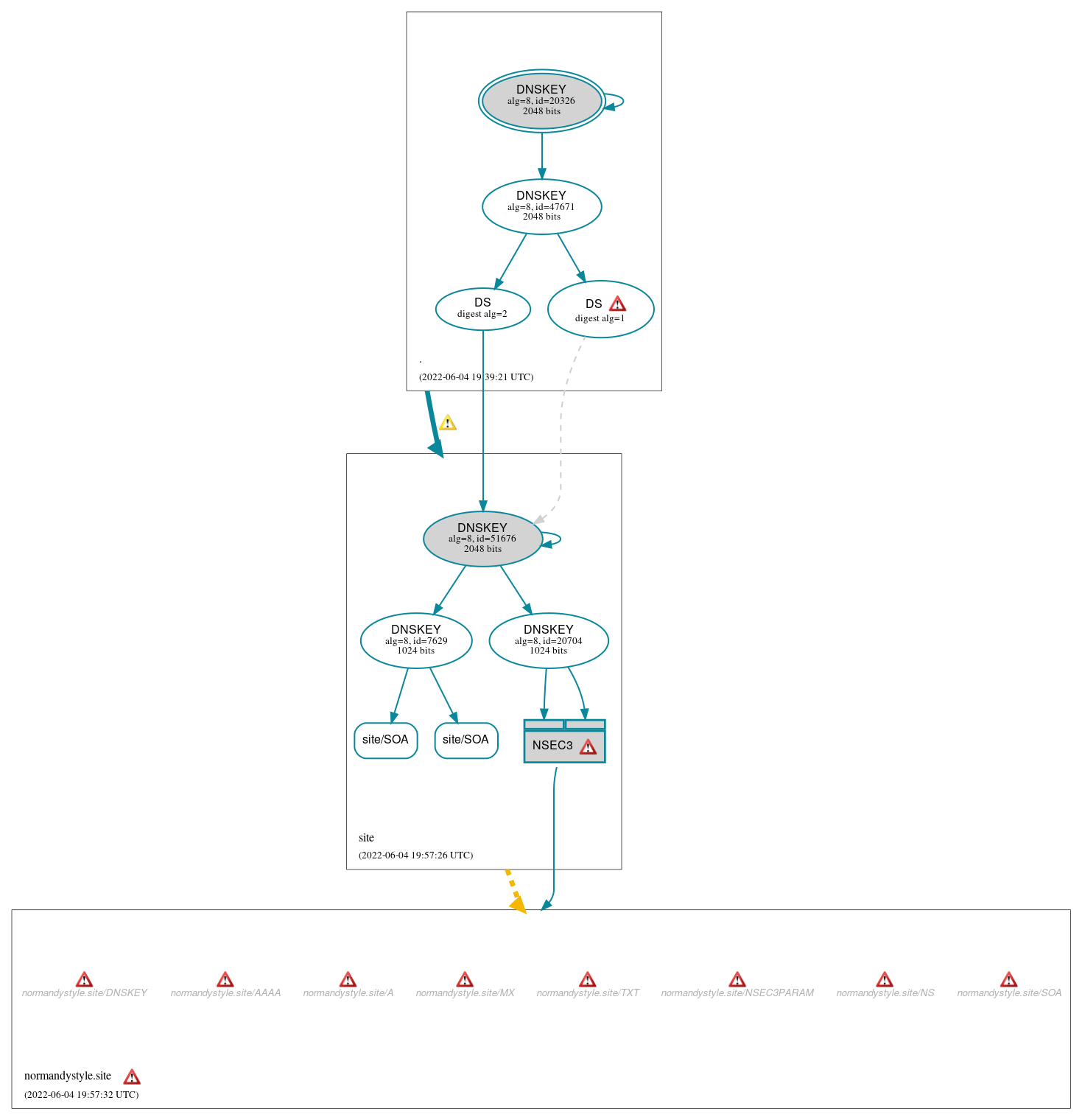
DNSSEC Authentication Chain
 RRset status
RRset status
Secure (2)
- site/SOA
- site/SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (8)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 47671)
- NSEC3 proving non-existence of normandystyle.site/DS
- site/DNSKEY (alg 8, id 20704)
- site/DNSKEY (alg 8, id 51676)
- site/DNSKEY (alg 8, id 7629)
- site/DS (alg 8, id 51676)
- site/DS (alg 8, id 51676)
 Delegation status
Delegation status
Lame (1)
- site to normandystyle.site
Secure (1)
- . to site
 Notices
Notices
Errors (11)
- normandystyle.site zone: The server(s) responded over TCP with a malformed response or with an invalid RCODE. (163.44.242.7, 163.44.242.8)
- normandystyle.site zone: The server(s) responded over UDP with a malformed response or with an invalid RCODE. (163.44.242.7, 163.44.242.8)
- normandystyle.site/A: The response had an invalid RCODE (REFUSED). (163.44.242.7, 163.44.242.8, UDP_-_EDNS0_4096_D_KN)
- normandystyle.site/AAAA: The response had an invalid RCODE (REFUSED). (163.44.242.7, 163.44.242.8, UDP_-_EDNS0_4096_D_KN)
- normandystyle.site/DNSKEY: The response had an invalid RCODE (REFUSED). (163.44.242.7, 163.44.242.8, UDP_-_EDNS0_4096_D_KN, UDP_-_EDNS0_512_D_KN)
- normandystyle.site/MX: The response had an invalid RCODE (REFUSED). (163.44.242.7, 163.44.242.8, UDP_-_EDNS0_4096_D_KN, UDP_-_EDNS0_512_D_KN)
- normandystyle.site/NS: The response had an invalid RCODE (REFUSED). (163.44.242.7, 163.44.242.8, UDP_-_EDNS0_4096_D_KN)
- normandystyle.site/NSEC3PARAM: The response had an invalid RCODE (REFUSED). (163.44.242.7, 163.44.242.8, UDP_-_EDNS0_4096_D_KN)
- normandystyle.site/SOA: The response had an invalid RCODE (REFUSED). (163.44.242.7, 163.44.242.8, TCP_-_EDNS0_4096_D_N)
- normandystyle.site/SOA: The response had an invalid RCODE (REFUSED). (163.44.242.7, 163.44.242.8, UDP_-_EDNS0_4096_D_KN, UDP_-_EDNS0_4096_D_KN_0x20)
- normandystyle.site/TXT: The response had an invalid RCODE (REFUSED). (163.44.242.7, 163.44.242.8, UDP_-_EDNS0_4096_D_KN)
Warnings (5)
- . to site: The following NS name(s) were found in the authoritative NS RRset, but not in the delegation NS RRset (i.e., in the . zone): g.nic.site
- site/DS (alg 8, id 51676): DNSSEC specification prohibits signing with DS records that use digest algorithm 1 (SHA-1).
- site/DS (alg 8, id 51676): DNSSEC specification prohibits signing with DS records that use digest algorithm 1 (SHA-1).
- site/DS (alg 8, id 51676): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset.
- site/DS (alg 8, id 51676): DS records with digest type 1 (SHA-1) are ignored when DS records with digest type 2 (SHA-256) exist in the same RRset.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.