cyberthreat.id
Updated:
2025-01-28 09:07:37 UTC (328 days ago)
Update now
Notices
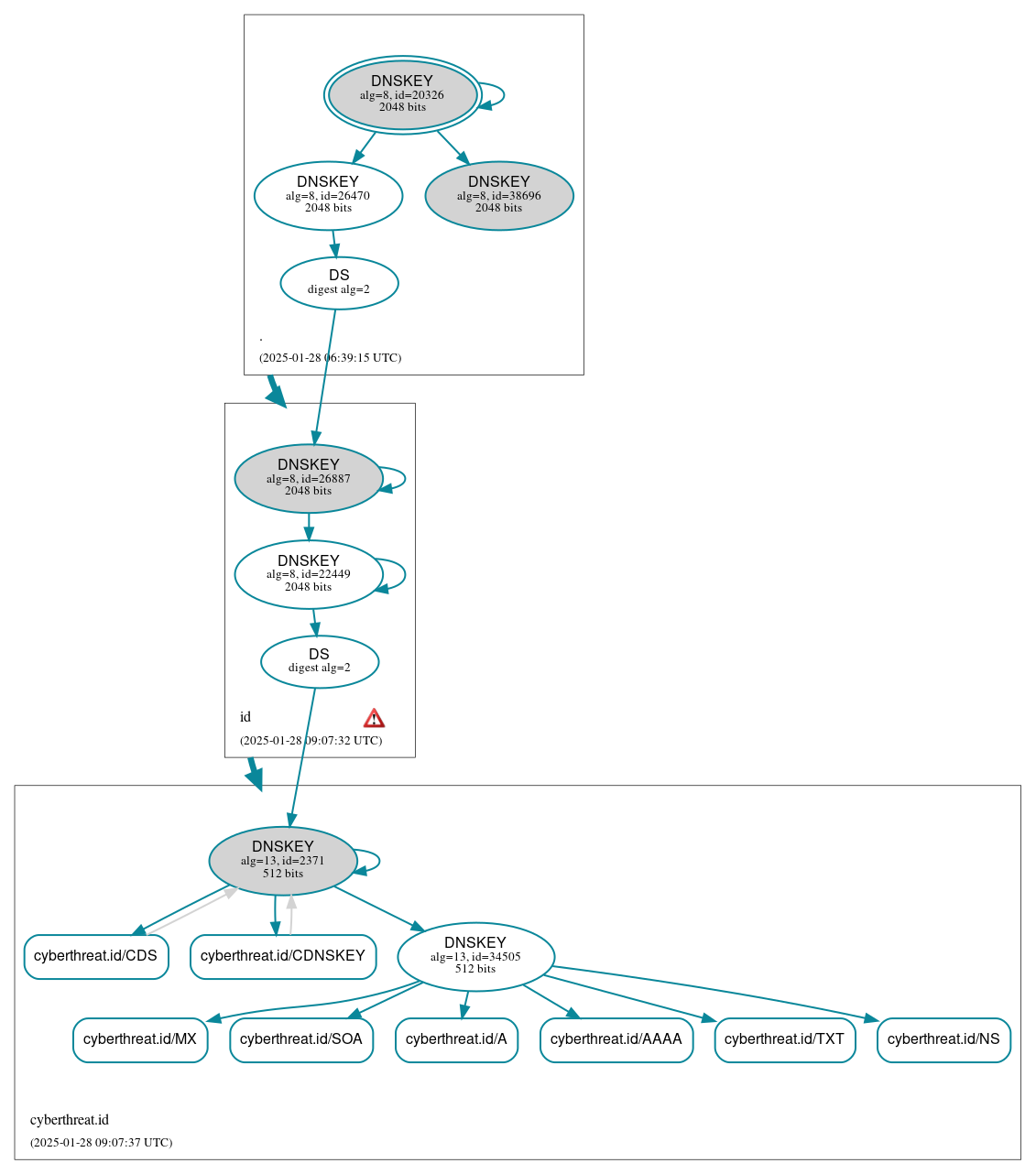
DNSSEC Authentication Chain
 RRset status
RRset status
Secure (8)
- cyberthreat.id/A
- cyberthreat.id/AAAA
- cyberthreat.id/CDNSKEY
- cyberthreat.id/CDS
- cyberthreat.id/MX
- cyberthreat.id/NS
- cyberthreat.id/SOA
- cyberthreat.id/TXT
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (9)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 26470)
- ./DNSKEY (alg 8, id 38696)
- cyberthreat.id/DNSKEY (alg 13, id 2371)
- cyberthreat.id/DNSKEY (alg 13, id 34505)
- cyberthreat.id/DS (alg 13, id 2371)
- id/DNSKEY (alg 8, id 22449)
- id/DNSKEY (alg 8, id 26887)
- id/DS (alg 8, id 26887)
 Delegation status
Delegation status
Secure (2)
- . to id
- id to cyberthreat.id
 Notices
Notices
Errors (1)
- id zone: The server(s) were not responsive to queries over UDP. See RFC 1035, Sec. 4.2. (2402:ee80:d::d)





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.