bogus.d3a10n3.rootcanary.net
Updated:
2020-04-19 18:09:27 UTC (2070 days ago)
Update now
Notices
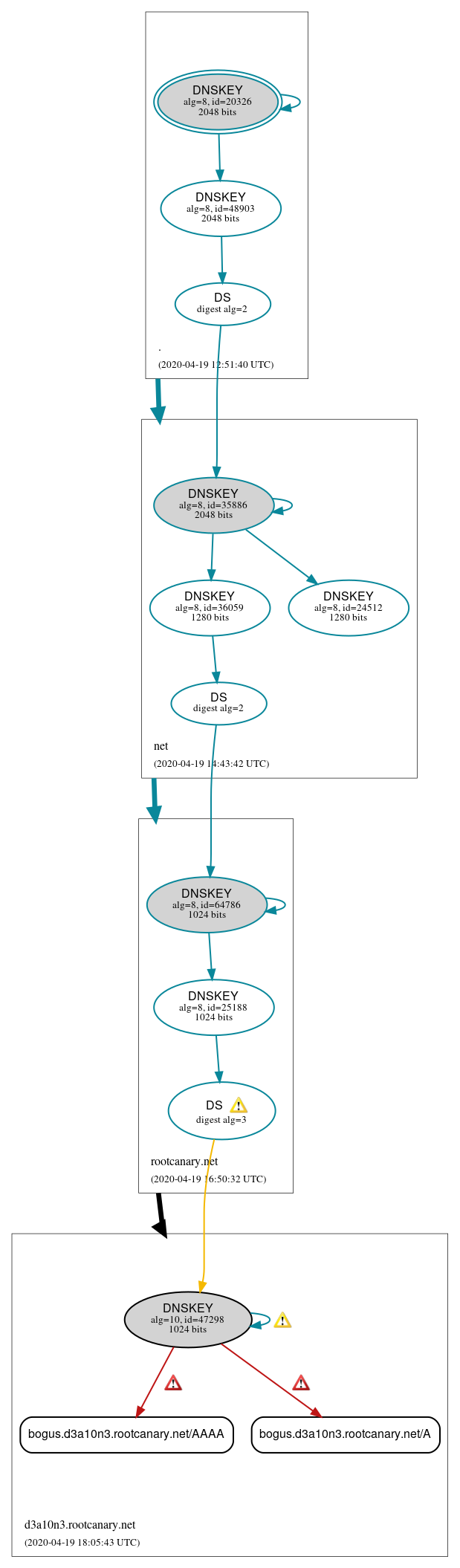
DNSSEC Authentication Chain
 RRset status
RRset status
Insecure (2)
- bogus.d3a10n3.rootcanary.net/A
- bogus.d3a10n3.rootcanary.net/AAAA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Insecure (1)
- d3a10n3.rootcanary.net/DNSKEY (alg 10, id 47298)
Secure (10)
- ./DNSKEY (alg 8, id 20326)
- ./DNSKEY (alg 8, id 48903)
- d3a10n3.rootcanary.net/DS (alg 10, id 47298)
- net/DNSKEY (alg 8, id 24512)
- net/DNSKEY (alg 8, id 35886)
- net/DNSKEY (alg 8, id 36059)
- net/DS (alg 8, id 35886)
- rootcanary.net/DNSKEY (alg 8, id 25188)
- rootcanary.net/DNSKEY (alg 8, id 64786)
- rootcanary.net/DS (alg 8, id 64786)
 Delegation status
Delegation status
Insecure (1)
- rootcanary.net to d3a10n3.rootcanary.net
Secure (2)
- . to net
- net to rootcanary.net
 Notices
Notices
Errors (3)
- RRSIG bogus.d3a10n3.rootcanary.net/A alg 10, id 47298: The cryptographic signature of the RRSIG RR does not properly validate. See RFC 4035, Sec. 5.3.3.
- RRSIG bogus.d3a10n3.rootcanary.net/AAAA alg 10, id 47298: The cryptographic signature of the RRSIG RR does not properly validate. See RFC 4035, Sec. 5.3.3.
- d3a10n3.rootcanary.net/CNAME has errors; select the "Denial of existence" DNSSEC option to see them.
Warnings (8)
- RRSIG bogus.d3a10n3.rootcanary.net/A alg 10, id 47298: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 10 (RSASHA512). See RFC 8624, Sec. 3.1.
- RRSIG bogus.d3a10n3.rootcanary.net/AAAA alg 10, id 47298: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 10 (RSASHA512). See RFC 8624, Sec. 3.1.
- RRSIG d3a10n3.rootcanary.net/DNSKEY alg 10, id 47298: DNSSEC implementers are recommended against implementing signing with DNSSEC algorithm 10 (RSASHA512). See RFC 8624, Sec. 3.1.
- d3a10n3.rootcanary.net/DS (alg 10, id 47298): DNSSEC implementers are prohibited from implementing signing with DS algorithm 3 (GOST 34.11-94). See RFC 8624, Sec. 3.2.
- d3a10n3.rootcanary.net/DS (alg 10, id 47298): DNSSEC implementers are prohibited from implementing signing with DS algorithm 3 (GOST 34.11-94). See RFC 8624, Sec. 3.2.
- d3a10n3.rootcanary.net/DS (alg 10, id 47298): Generating cryptographic hashes using algorithm 3 (GOST 34.11-94) is not supported by this code, so the cryptographic status of the DS RR is unknown. See RFC 4035, Sec. 5.2.
- d3a10n3.rootcanary.net/DS (alg 10, id 47298): Generating cryptographic hashes using algorithm 3 (GOST 34.11-94) is not supported by this code, so the cryptographic status of the DS RR is unknown. See RFC 4035, Sec. 5.2.
- d3a10n3.rootcanary.net/CNAME has warnings; select the "Denial of existence" DNSSEC option to see them.





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.