or.ke
Updated:
2022-11-30 21:22:20 UTC (522 days ago)
Update now
Notices
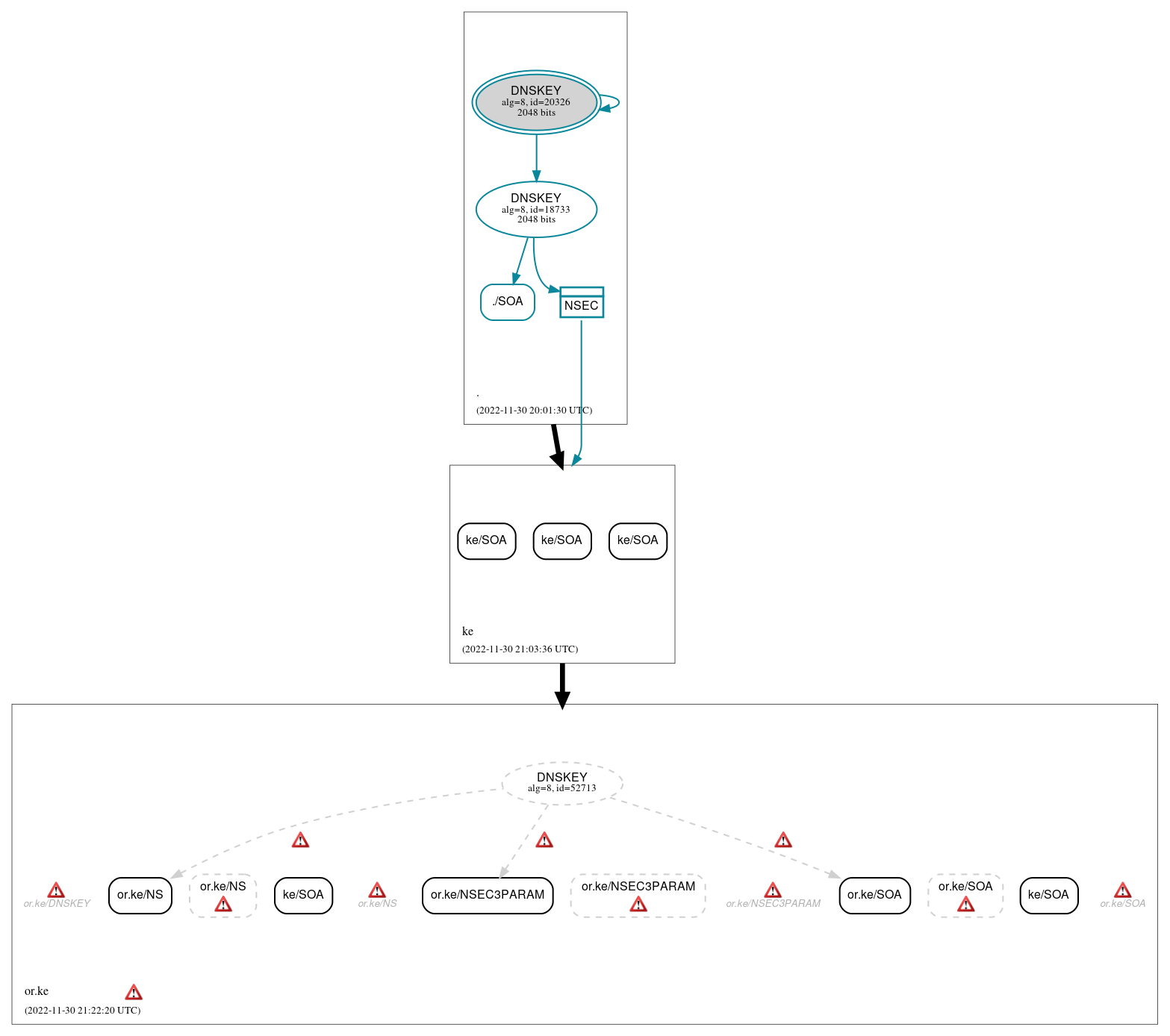
DNSSEC Authentication Chain
 RRset status
RRset status
Insecure (11)
- ke/SOA
- ke/SOA
- ke/SOA
- ke/SOA
- ke/SOA
- or.ke/NS
- or.ke/NS (NODATA)
- or.ke/NSEC3PARAM
- or.ke/NSEC3PARAM (NODATA)
- or.ke/SOA
- or.ke/SOA (NODATA)
Secure (1)
- ./SOA
 DNSKEY/DS/NSEC status
DNSKEY/DS/NSEC status
Secure (3)
- ./DNSKEY (alg 8, id 18733)
- ./DNSKEY (alg 8, id 20326)
- NSEC proving non-existence of ke/DS
Non_existent (1)
- or.ke/DNSKEY (alg 8, id 52713)
 Delegation status
Delegation status
Insecure (2)
- . to ke
- ke to or.ke
 Notices
Notices
Errors (20)
- RRSIG or.ke/NS alg 8, id 52713: The Signature Expiration field of the RRSIG RR (2022-09-05 14:18:25+00:00) is 86 days in the past.
- RRSIG or.ke/NSEC3PARAM alg 8, id 52713: The Signature Expiration field of the RRSIG RR (2022-09-03 19:03:18+00:00) is 88 days in the past.
- RRSIG or.ke/SOA alg 8, id 52713: The Signature Expiration field of the RRSIG RR (2022-09-14 01:11:47+00:00) is 77 days in the past.
- or.ke zone: The server(s) responded over TCP with a malformed response or with an invalid RCODE. (196.216.162.70)
- or.ke zone: The server(s) responded over UDP with a malformed response or with an invalid RCODE. (196.216.162.70)
- or.ke zone: The server(s) were not responsive to queries over TCP. (196.216.168.22, 2001:500:14:6007:ad::1)
- or.ke zone: The server(s) were not responsive to queries over UDP. (2001:43f8:e0:1::70)
- or.ke/DNSKEY: No response was received from the server over TCP (tried 7 times). (196.216.168.22, TCP_-_EDNS0_4096_D)
- or.ke/DNSKEY: No response was received from the server over UDP (tried 4 times). (196.216.168.22, UDP_-_EDNS0_512_D_KN)
- or.ke/DNSKEY: The response had an invalid RCODE (SERVFAIL). (196.216.162.70, UDP_-_EDNS0_512_D_KN, UDP_-_NOEDNS_)
- or.ke/NS (NODATA): An SOA RR with owner name (ke) not matching the zone name (or.ke) was returned with the NODATA response. (147.135.106.237, 185.28.194.194, 185.38.108.108, 196.1.4.3, 196.1.4.130, 196.216.168.22, 198.32.67.9, 204.61.216.7, 2001:500:14:6007:ad::1, 2001:43f8:10:0:50c0:a8ff:feee:30, 2604:2dc0:200:2eb::237, UDP_-_EDNS0_4096_D_KN)
- or.ke/NS: No response was received from the server over UDP (tried 12 times). (2001:43f8:e0:1::70, UDP_-_NOEDNS_)
- or.ke/NS: The response had an invalid RCODE (SERVFAIL). (196.216.162.70, UDP_-_NOEDNS_)
- or.ke/NSEC3PARAM (NODATA): An SOA RR with owner name (ke) not matching the zone name (or.ke) was returned with the NODATA response. (147.135.106.237, 185.28.194.194, 185.38.108.108, 196.1.4.3, 196.1.4.130, 198.32.67.9, 204.61.216.7, 2001:500:14:6007:ad::1, 2001:43f8:10:0:50c0:a8ff:feee:30, 2604:2dc0:200:2eb::237, UDP_-_EDNS0_4096_D_KN)
- or.ke/NSEC3PARAM: No response was received from the server over UDP (tried 12 times). (196.216.168.22, UDP_-_NOEDNS_)
- or.ke/NSEC3PARAM: The response had an invalid RCODE (SERVFAIL). (196.216.162.70, UDP_-_NOEDNS_)
- or.ke/SOA (NODATA): An SOA RR with owner name (ke) not matching the zone name (or.ke) was returned with the NODATA response. (147.135.106.237, 185.28.194.194, 185.38.108.108, 196.1.4.3, 196.1.4.130, 196.216.168.22, 198.32.67.9, 204.61.216.7, 2001:500:14:6007:ad::1, 2001:43f8:10:0:50c0:a8ff:feee:30, 2001:43f8:120::22, 2604:2dc0:200:2eb::237, TCP_-_EDNS0_4096_D_N, UDP_-_EDNS0_4096_D_KN, UDP_-_EDNS0_4096_D_KN_0x20)
- or.ke/SOA: No response was received from the server over TCP (tried 3 times). (196.216.168.22, 2001:500:14:6007:ad::1, TCP_-_EDNS0_4096_D_N)
- or.ke/SOA: The response had an invalid RCODE (SERVFAIL). (196.216.162.70, TCP_-_NOEDNS_)
- or.ke/SOA: The response had an invalid RCODE (SERVFAIL). (196.216.162.70, UDP_-_NOEDNS_, UDP_-_NOEDNS__0x20)





 JavaScript is required to make the graph below interactive.
JavaScript is required to make the graph below interactive.